In an increasingly online world, where trust is both a currency and a vulnerability, threat actors seek to manipulate human behavior and take advantage of people’s tendency to want to be helpful. In this infographic, we’ll explore social engineering including why threat actors value professional identities above all others while walking you through some of the ways they manipulate human nature to achieve their goals.
Agents built into your everyday workflow. Read the announcement
Feeding from the trust economy: social engineering fraud

Social engineering and the criminal allure of phishing
Approximately 901 percent of phishing attacks involve social engineering tactics designed to manipulate victims—usually via email—into revealing sensitive information, clicking malicious links, or opening malicious files. Phishing attacks are cost-effective for attackers, adaptable to help evade prevention measures, and boast high success rates.
The levers of human behavior
“The hallmark of a phishing email is the attachment of some type of time frame. They want to push you to make a decision in an abbreviated time.”
Emotion
Emotional manipulation can give cyber attackers an upper hand, since humans are more likely to take risky actions in a heightened emotional state, especially if fear, guilt, or anger are involved.
Example: Emotional Manipulation
“The most effective lure I have ever seen was a very short email that said we have been contracted by your spouse to prepare your divorce papers. Click the link to download your copy.”
Habit
Criminals are keen observers of behavior, and they pay special attention to the kinds of habits and routines people perform “on autopilot,” without too much extra thought.
Example: Common habit
“Threat actors adapt to the rhythms of business. They’re great at deploying lures that make sense in the context we normally receive them.”
The boundary between an employee’s personal and professional persona can sometimes converge. An employee may use their work email for personal accounts they use for work. Threat actors sometimes try to take advantage of that by reaching out with the appearance of being one of these programs so as to gain access to an employee’s corporate information.

“In email phishing scams, cybercriminals check their “lures” for corporate email addresses. Personal webmail addresses aren’t worth their time. Work addresses are more valuable, so they’ll put more resources and focus with hands-on-keyboard to customizing attacks for those accounts.”
The “long con”
- Investigation: Engineers identify a target and gather background information, like potential points of entry or security protocols.
- Infiltrate: The engineers focus on establishing trust with the target. They spin a story, hook the target, and take control of the interaction to steer it in a way that benefits the engineer.
- Exploit: Social engineers obtain the target’s information over time. Typically, the target hands over this information willingly, and engineers may use this to their advantage to gain access to even more confidential information.
- Disengage: A social engineer will bring the interaction to a natural end. A skilled engineer will do this without making the target feel suspicious at all
BEC attacks stand apart in the cybercrime industry for their emphasis on social engineering and the art of deception. Successful BEC attacks cost organizations hundreds of millions of dollars annually. In 2022, the Federal Bureau of Investigation (FBI) Internet Crime Complaint Center recorded adjusted losses of more than USD$2.7 billion for 21,832 BEC complaints filed.4
Top targets for BEC are executives and other senior leaders, finance managers, human resources staff with access to employee records like Social Security numbers, tax statements, or other personal identifiable information. New employees, perhaps less likely to verify unfamiliar email requests, are also targeted.
Nearly all forms of BEC attacks are on the rise. Common BEC attack types include:5
- Direct Email Compromise (DEC): Compromised email accounts are used to socially engineer in-house or third-party accounting roles to wire funds to the attacker’s bank account or change payment information for an existing account.
- Vendor Email Compromise (VEC): Social engineering of an existing supplier relationship by hijacking a payment-related email and impersonating company employees to convince a supplier to redirect outstanding payment to an illicit bank account.
- False Invoice Scam: A mass social engineering scam that exploits well-known business brands to convince companies to pay fake invoices.
- Attorney Impersonation: The exploitation of trusted relationships with large, well-known law firms to increase credibility with executives of small companies and start-ups to complete payment of outstanding invoices, particularly prior to significant events like initial public offerings. Payment redirection to an illicit bank account occurs once an agreement on payments terms is reached.
Octo Tempest
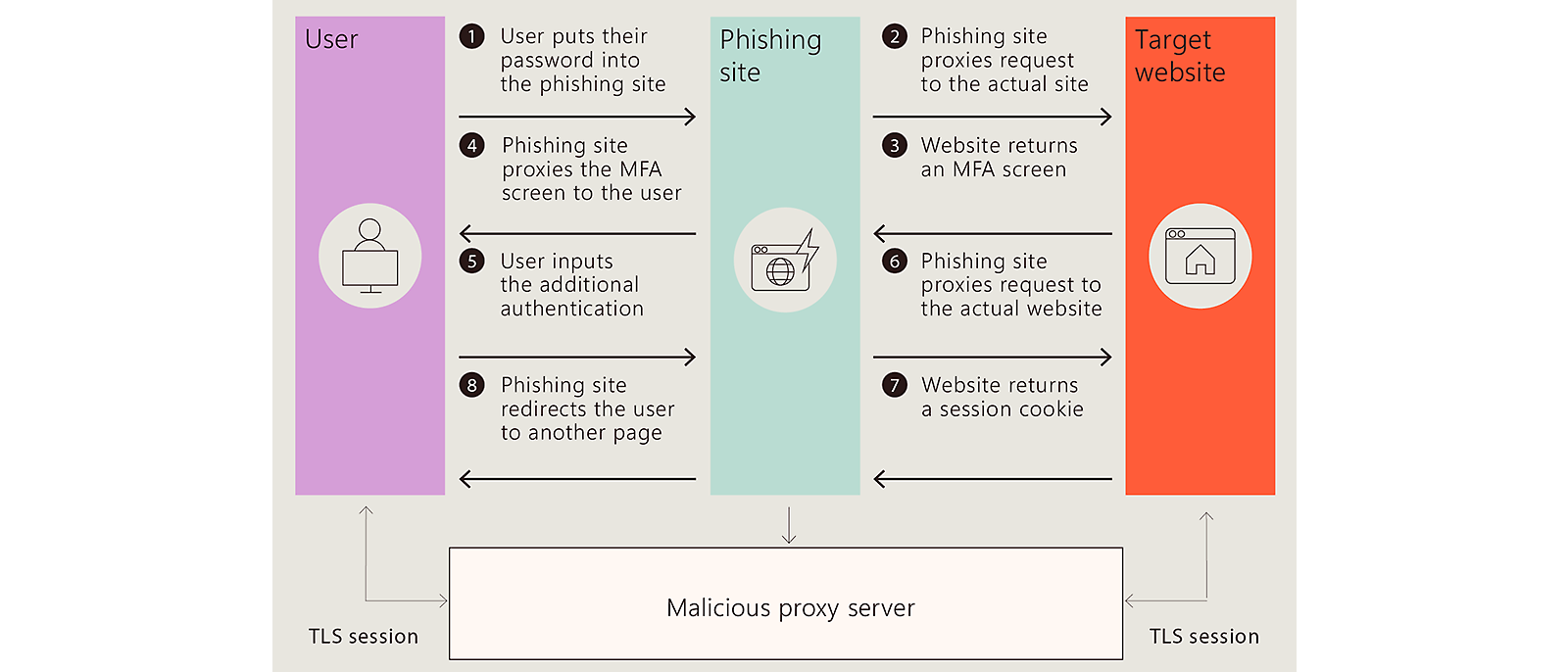
Octo Tempest is a financially motivated collective of native English-speaking threat actors known for launching wide-ranging campaigns that prominently feature adversary-in-the-middle (AiTM) techniques, social engineering, and SIM swapping capabilities.
Diamond Sleet
In August 2023, Diamond Sleet conducted a software supply chain compromise of German software provider JetBrains that compromised servers for software building, testing, and deployment processes. Because Diamond Sleet has successfully infiltrated build environments in the past, Microsoft assesses that this activity poses a particularly high risk to organizations who are affected.
Sangria Tempest6
Sangria Tempest, also known as FIN, is known for targeting the restaurant industry, stealing payment card data. One of their most effective lures involves an accusation of food poisoning, the details of which can be viewed upon the opening of a malicious attachment.
Sangria Tempest, who is primarily Eastern European, have used underground forums to recruit native English speakers, who are trained on how to call stores in the delivery of the email lure. The group has stolen tens of millions of payment card data through that process.
Midnight Blizzard
Midnight Blizzard is a Russia-based threat actor known to primarily target governments, diplomatic entities, non-government organizations (NGOs), and IT service providers primarily in the US and Europe.
Midnight Blizzard leverages Teams messages to send lures that attempt to steal credentials from a targeted organization by engaging a user and eliciting approval of multifactor authentication (MFA) prompts.
Did you know?
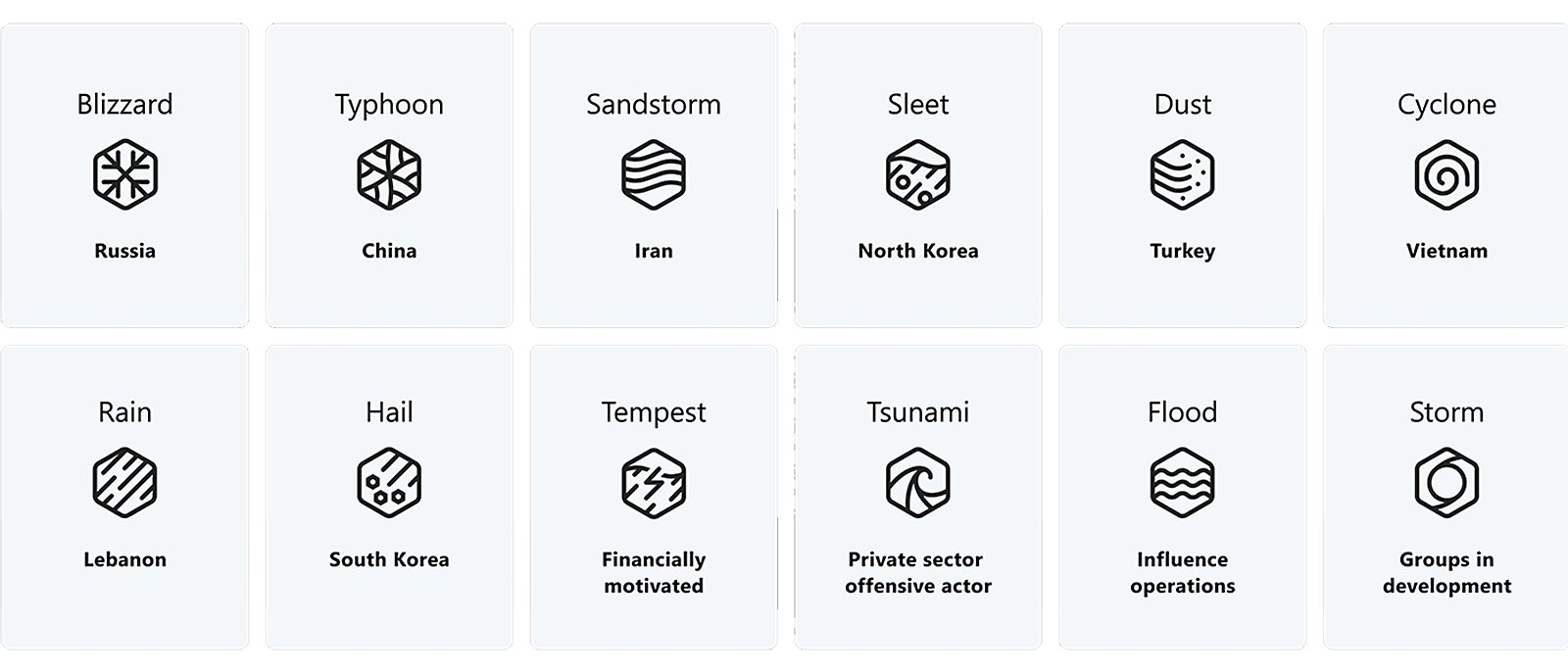
Microsoft’s threat actor naming strategy has shifted to a new naming taxonomy for threat actors drawing inspiration from weather-related themes.
While social engineering attacks can be sophisticated, there are things you can do to help prevent them.7 If you’re smart about your privacy and security, you can beat attackers at their own game.
First, instruct users to keep their personal accounts personal and not to blend them with work email or work-related tasks.
Also, be sure to enforce the use of MFA. Social engineers are typically seeking information like login credentials. By enabling MFA, even if an attacker gets your username and password, they still won’t be able to gain access to your accounts and personal information.8
Don’t open emails or attachments from suspicious sources. If a friend sends you a link that you need to click urgently, confirm with your friend whether the message was really from them. Pause and ask yourself if the sender is who they say they are before clicking anything.
Pause and verify
Be wary of offers that are too good to be true. You can’t win a sweepstakes you didn’t enter, and no foreign royalty is going to leave you a large amount of money. If it seems too tempting, do a quick search to determine if the offer is legitimate or a trap.
Don’t overshare online. Social engineers need their targets to trust them for their scams to work. If they can find your personal details from your social media profiles, they can use it to help make their scams seem more legitimate.
Secure your computers and devices. Use antivirus software, firewalls, and email filters. In case a threat does make its way to your device, you’ll have protection in place to help keep your information safe.
“When you get a questionable phone call or email, the key is to just slow down and verify. People make mistakes when they act too quickly, so it’s important to remind employees that they don’t have to react right away these kinds of situations.”
Learn more on how to help protect your organization by watching The risk of trust: Social engineering threats and cyber defense.
- [2]Content in this section sourced from https://go.microsoft.com/fwlink/?linkid=2263229
- [6]Waymon Ho, Around 27:32,https://go.microsoft.com/fwlink/?linkid=2263333
- [7]Note: Content comes from https://go.microsoft.com/fwlink/?linkid=2263229




Follow Microsoft Security