This is the first in a blog series discussing the tools, techniques, and procedures that the Microsoft Detection and Response Team (DART) use to investigate cybersecurity incidents at our customer organizations. Today, we introduce the team and give a brief overview of each of the tools that utilize the power of the cloud. In upcoming posts, we’ll cover each tool in-depth and elaborate on techniques and procedures used by the team.
Key lessons learned from DART’s investigation evolution
DART’s investigation procedures and technology have evolved over 14 years of assisting our customers during some of the worst hack attacks on record. Tools have evolved from primarily bespoke (custom) tools into a blend of commercially available Microsoft detection solutions plus bespoke tools, most of which extend the core Microsoft detection capabilities. The team contributes knowledge and technology back to the product groups, who leverage that experience into our products, so our customers can benefit from our (hard-won) lessons learned during our investigations.
This experience means that DART’s tooling and communication requirements during incident investigations tend to be a bit more demanding than most in-house teams, given we’re often working with complex global environments. It’s not uncommon that an organization’s ability to detect and respond to security incidents is inadequate to cope with skilled attackers who will spend days and weeks profiling the organization and its employees. Consequently, we help organizations across many different industry verticals and from those experiences we have collated some key lessons:
- Detection is critical (and weak)—One of the first priorities when the team engages to assist with an incident investigation at a customer site is to increase the detection capability of that organization. Over the years, we’ve seen that industry-wide detection has stayed the weakest of the Protect, Detect, Respond triad. While the average dwell time numbers are trending downward, it’s still measured in days (usually double digit numbers) and days of access to your systems is plenty of time to do massive damage.
- Inadequate auditing—More often than not, DART finds that organizations don’t turn on auditing or have misconfigured auditing with the result that there is not a full record of attacker activities. See auditing best practices for Active Directory and Office 365. In addition, given the current prolific use of weaponized PowerShell scripts by attackers, we strongly recommend implementing PowerShell auditing.
- Static plus active containment—Static containment (protection) controls can never be 100 percent successful against skilled human attackers, so we need to add in an active containment component that can detect and contain those attackers at the edge and as they move around the environment. This second part is crucial—as they move around the environment—we need to move away from the traditional mindset of “Time to Detect” and implement a “Time to Remediate” approach with active containment procedures to disrupt attackers’ abilities to realize their objective once in the environment. Of course, attackers that have been in the organization for a very long time require more involved investigation and planning for an eviction event to be successful and lessen any potential impact to the organization.
These lessons have significantly influenced the methodology and toolsets we use in DART as we engage with our customers. In this blog series, we’ll share lessons learned and best practices of organizations and incident responders to help ensure readiness.
Observe-Orient-Decide-Act (OODA) framework
Before we can act in any meaningful way, we need to observe attacker activities, so we can orient ourselves and decide what to do. Orientation is the most critical step in the Observe-Orient-Decide-Act (OODA) framework developed by John Boyd and overviewed in this OODA article. Wherever possible, the team will light up several tools in the organization, installing the Microsoft Management Agent (MMA) and trial versions of the Microsoft Threat Protection suite, which includes Microsoft Defender ATP, Azure ATP, Office 365 ATP, and Microsoft Cloud App Security (our Cloud Access Security Broker (CASB) solution named illustrated in Figure 1). Why? Because these technologies were developed specifically to form an end-to-end picture across the attacker cyber kill-chain framework (reference Lockheed Martin) and together work swiftly to gather indicators of anomaly, attack, and compromise necessary for successful blocking of the attacker.
The Microsoft ATP platform of tools are used extensively by the Microsoft Corporate IT security operations center (SOC) in our Cyber Defence Operations Center (CDOC), whose slogan is “Minutes Matter.” Using these technologies, the CDOC has dropped their time to remediate incidents from hours to minutes—a game changer we’ve replicated at many of our customers.
Microsoft Threat Protection
The Microsoft Threat Protection platform includes Microsoft Defender ATP, Azure ATP, Office 365 ATP, as well as additional services that strengthen security for specific attack vectors, while adding security for attack vectors that would not be covered by the ATP solutions alone. Read Announcing Microsoft Threat Protection for more information. In this blog, we focus on the tools that give DART a high return on investment in terms of speed to implement versus visibility gained.
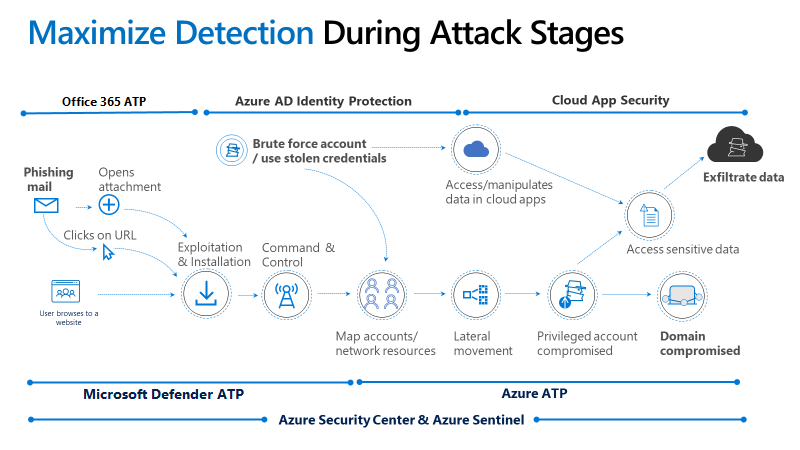
Figure 1. Microsoft Threat Protection and the cyber kill-chain.
Although the blog series discusses Microsoft technologies preferentially, the intent here is not to replicate data or signals—the team uses what the customer has—but to close gaps where the organization might be missing signal. With that in mind, let’s move on to a brief discussion of the tools.
Horizontal tools: Visibility across the cyber kill-chain
Horizonal tools include Azure Sentinel and Azure Security Center:
- Azure Sentinel—New to DART’s arsenal is Azure Sentinel—the first cloud-native SIEM (security investigation and event management). Over the past few months, DART has deployed Azure Sentinel as a mechanism to combine the different signal sets in what we refer to as a SIEM and SOAR as a service. SOAR, which stands for security orchestration and automation, is indispensable in its capability to respond to attacker actions with speed and accuracy. Our intention is not to replicate a customer SIEM but to use the power of the cloud and machine learning to quickly combine alerts across the cyber kill-chain in a fusion model to lessen the time it takes an investigator to understand what the attacker is doing.
Importantly, machine learning gives DART the ability to aggregate diverse signals and get an end-to-end picture of what is going on quickly and to act on that information. In this way, information important to the investigation can be forwarded to the existing SIEM, allowing for efficient and speedy analysis utilizing the power of the cloud.
- Azure Security Center—DART also onboards the organization into Azure Security Center, if not already enabled for the organization. This tool significantly adds to our ability to investigate and pivot across the infrastructure, especially given the fact that many organizations don’t yet have Windows 10 devices deployed throughout. Security Center also does much more with machine learning for next-generation detection and simplifying security management across clouds and platforms (Windows/Linux).
DART’s focus for the tool is primarily on the log analytics capabilities that allow us to pivot our investigation and, furthermore, utilize the recommended hardening suggestions during our rapid recovery work. We also recommend the implementation of Security Center proactively, as it gives clear security recommendations that an organization can implement to secure their on-premises and cloud infrastructures. See Azure Security Center FAQs for more information.
Vertical tools: Depth visibility in designated areas of the cyber kill-chain
Vertical tools include Azure ATP, Office 365 ATP, Microsoft Defender ATP, Cloud App Security, and custom tooling:
- Azure ATP—The Verizon Data Breach Report of 2018 reported that 81 percent of breaches are caused by compromised credentials. Every incident that DART has responded to over the last few years has had some component of credential theft; consequently Azure ATP is one of the first tools we implement when we get to a site—before, if possible—to get insight into what users and entities are doing in the environment. This allows us to utilize built-in detections to determine suspicious behaviour, such as suspicious changes of identity metadata and user privileges.
- Office 365 ATP—With approximately 90 percent of all attacks starting with a phishing email, having ways to detect when a phishing email makes it past email perimeter defences is critical. DART investigators are always interested in which mechanism the attacker compromised the environment—simply so we can be sure to block that vector. We use Office 365 ATP capabilities— such as security playbooks and investigation graphs—to investigate and remediate attacks faster.
- Microsoft Defender ATP—If the organization has Windows 10 devices, we can implement Microsoft Defender ATP (previously Windows Defender ATP)—a cloud-based solution that leverages a built-in agent in Windows 10. Otherwise, we’ll utilize MMA to gather information from older versions of Windows and Linux machines and pull that information into our investigation. This makes it possible to detect attacker activities, aggregate this information, and prioritize the investigation of detected activity.
- Cloud App Security—Cloud App Security is a multi-mode cloud access security broker that natively integrates with the other tools DART deploys, giving access to sophisticated analytics to identify and combat cyberthreats across the organizations. This allows us to detect any malicious activity using cloud resources that the attacker might be undertaking. Cloud App Security, combined with Azure ATP, allows us to see if the attacker is exfiltrating data from the organization, and also allows organizations to proactively determine and assess any shadow IT they may be unaware of.
- Custom tooling—Bespoke custom tooling is deployed depending on attacker activities and the software present in the organization. Examples include infrastructure health-check tools, which allow us to check for any modification of Microsoft technologies—such as Active Directory, Microsoft’s public key infrastructure (PKI), and Exchange health (where Office 365 is not in use) as well as tools designed to detect use of specific specialist attack vectors and persistence mechanisms. Where machines are in frame for a deeper investigation, we normally utilize a tool that runs against a live machine to acquire more information about that machine, or even run a full disk acquisition forensic tool, depending on legal requirements.
Together, the vertical tools give us unparalleled view into what is happening in the organization. These signals can be collated and aggregated into both Security Center and Azure Sentinel, where we can pull other data sources as available to the organization’s SOC.
Figure 2 represents how we correlate the signal and utilize machine learning to quickly identify compromised entities inside the organization.
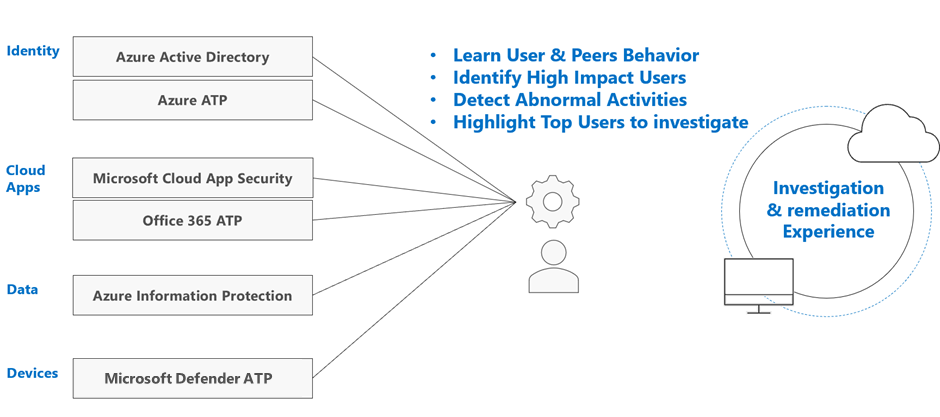
Figure 2. Combining signals to identify compromised users and devices.
This gives us a very swift way to bubble up anomalous activity and allows us to rapidly orient ourselves against attacker activity. In many cases, we can then use automated playbooks to block attacker activity once we understand the attacker’s tools, techniques, and procedures; but that will be the subject of another post.
Next up—how Azure Sentinel helps DART
Today, in Part 1 of our blog series, we introduced the suite of tools used by DART and the Microsoft CDOC to rapidly detect attacker activity and actions—because in the case of cyber incident investigations, minutes matter. In our next blog we’ll drill down into Azure Sentinel capabilities to highlight how it helps DART; stay posted!
Azure Sentinel
Intelligent security analytics for your entire enterprise.

Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.








