Zero Trust revolves around three key principles: verify explicitly, use least privileged access, and assume breach. Microsoft’s Advanced Compliance Solutions are an important part of Zero Trust.
This post applies a Zero Trust lens to protecting an organization’s sensitive data and maintaining compliance with relevant standards. Ultimately, Zero Trust architecture is a modern approach to security that focuses on security and compliance for assets regardless of their physical or network location, which contrasts with classic approaches that attempt to force all assets on a ‘secure’ and compliant network.
A Zero Trust strategy should start with Identity and Access Management. Microsoft built Azure Active Directory (AAD) to enable rapid Zero Trust adoption:
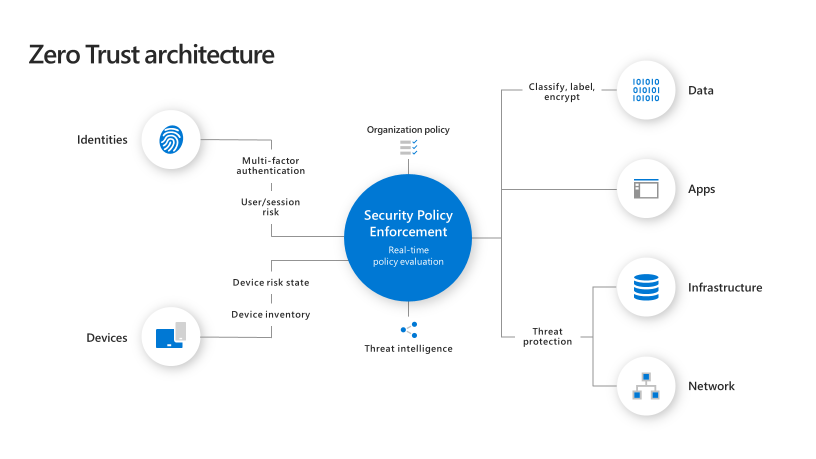
Architects focus on applying the Zero Trust principles to protect and monitor six technical pillars of the enterprise including:
- Identity
- Devices
- Applications and APIs
- Data
- Infrastructure
- Networks
In an integrated Microsoft Zero Trust solution, AAD and Microsoft Defender for Identity provide protection, monitoring, and trust insights in the User/Identity Pillar. Microsoft Defender for Endpoints and Intune protect and manage the Device. Azure Security Center and Azure Sentinel monitor, report, and provide automated playbooks to deal with events.
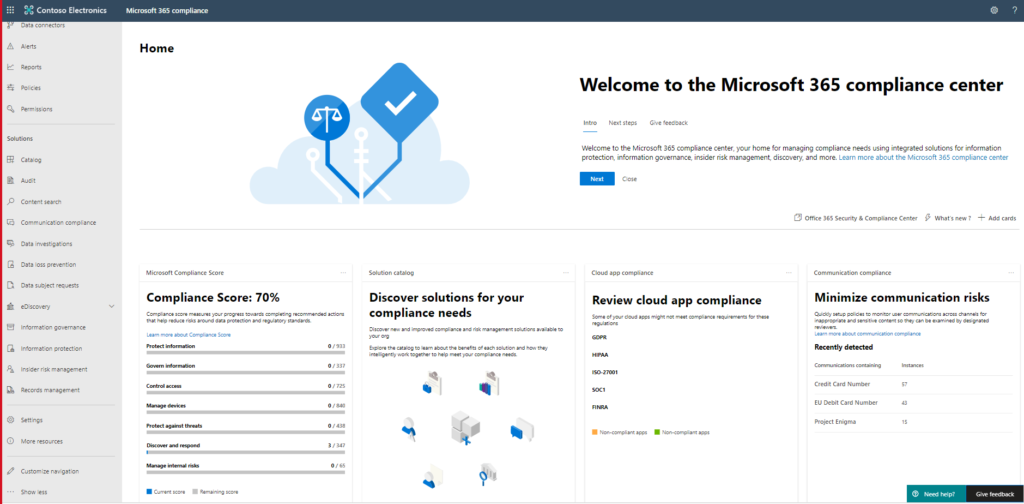
Microsoft’s Advanced Compliance solutions are foundational to Zero Trust as well, particularly when implemented to support Microsoft 365.
Microsoft Information Protection, Insider Risk Management, and Microsoft Cloud App Security are all part of a complete Zero Trust architecture.
Advanced Auditing can increase the visibility around insider or bad actor’s activities with sensitive data like documents and emails as well as increasing the period over which audit data is available for review.
Let’s look closer at these solutions:
- Microsoft Information Protection: Allows policy enforcement at the document level based on AAD identity. This protection is resident with the document throughout its lifecycle. It controls the identities, groups or organizations that can access the document, expires access to the document and controls what authorized users can do with the document e.g. view, print, cut and paste as well as other controls like enforced watermarking. These controls can be mandatory or can support users with suggested protection. The policy can be informed by machine learning, standard sensitivity data types (like social security numbers), regular expressions, keywords or exact data match. When users elect to apply different protection than recommended, their actions are tracked for later review. Documents can thus be protected throughout their lifecycle, wherever they may travel and to whomever they may be transmitted.
Microsoft Information Protection sensitivity labels are fully integrated with our data loss prevention solution, preventing movement of sensitive information at the boundary of the cloud, between Microsoft and third-party clouds, and at the device endpoint (e.g. laptop).
- Insider Risk Management: Applies machine learning to the signals available from Microsoft O365 tenant logs, integration with Microsoft Defender Advanced Threat Protection and an increasing number of Microsoft and third party relevant signals to alert on insiders such as employees or contractors who are misusing their access. Default policies are provided, and enterprises can customize policies to meet their needs including for specific projects or scoped to users deemed to be at high risk. These policies allow you to identify risky activities and mitigate these risks. Current areas of focus for the solution are:
- Leaks of sensitive data and data spillage
- Confidentiality violations
- Intellectual property (IP) theft
- Fraud
- Insider trading
- Regulatory compliance violations
These signals are visualized and actioned by other Microsoft solutions. Insider Risk Management uses its specialized algorithms and machine learning to correlate signal and expose Insider Risks in context. It also provides workflows and visualizations to manage cases.
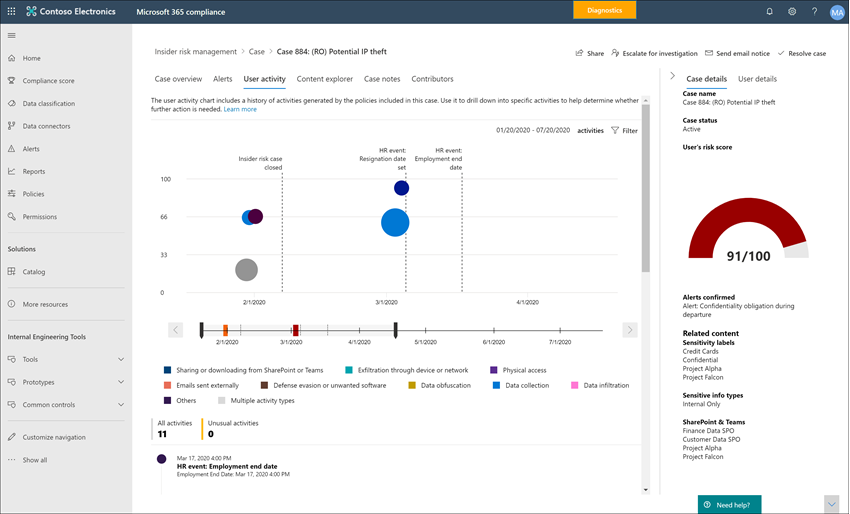
Insider Risk Management is integrated with AAD and acts on signals from Microsoft Information Protection as well as others in the tenant, providing additional security value from the systems already in place. The alerts generated by the system can be managed with the native case management features or surfaced to Azure Sentinel or third-party systems through the API.
- Microsoft Cloud App Security: Is a Cloud Access Security Broker that supports various deployment modes including log collection, API connectors, and reverse proxy. It provides rich visibility, granular control over data travel, and sophisticated analytics to identify and combat cyber threats across all Microsoft and third-party cloud services. It controls shadow IT. It can be used to govern the use of Microsoft and third-party clouds and the sensitive information placed there.

- Advanced Auditing for M365: Advanced Audit retains all Exchange, SharePoint, and Azure Active Directory audit records for a default of one year. You can retain audit logs for up to ten years. Crucial events for investigations, such as whether an attacker has accessed a mail message, whether a sensitive document is re-labeled and many other new log data types are part of this solution. Investigation playbooks will also shortly be part of this solution.
These Advanced Compliance solutions have native visibility into AAD, the Microsoft Tenant, and into each other. For example, Insider Risk Management has visibility into Microsoft Information Protection sensitivity labels. Microsoft Cloud App Security has visibility into and can act on sensitivity labels.
This visibility and machine learning run through the Microsoft Security and Advanced Compliance solutions, making them particularly well suited to a holistic Zero Trust architecture.