We are swiftly adapting to the lasting reality of a hybrid workforce, with the number of remote workers in the US expected to nearly double over the next five years, compared to pre-pandemic times. As a result, security teams are being challenged to rethink how to secure a growing and increasingly diverse portfolio of devices outside of the traditional boundaries of their organization. However, what has stayed constant during this time of change is the focus of adversaries to identify and take advantage of vulnerabilities that have been left unpatched or misconfigurations as a gateway to sensitive information. It stresses the need for a proactive approach to vulnerability management and a focus on an organization’s high-risk assets.
Microsoft’s Threat and Vulnerability Management (TVM) capabilities play a crucial role in monitoring an organization’s overall security posture, with devices being a key entry point for compromise if left exposed. It equips customers with real-time insights into risk with continuous vulnerability discovery, intelligent prioritization that takes business and threat context into account, and the ability to seamlessly remediate vulnerabilities with a single click. The recent Nobelium attack is only one example of a critical vulnerability, where TVM enabled customers to identify affected devices in their environment and take immediate action.
As threat and vulnerability management evolves, we continue to expand our coverage to include additional devices and OS platforms. Today, we are announcing that Microsoft’s Threat and Vulnerability Management capabilities now cover Linux operating systems, in addition to macOS and Windows—with support for Android and iOS planned for later this summer.
Organizations can now review recently discovered vulnerabilities within installed applications across the Linux OS and issue remediation tasks for all affected devices. Initial support is available for RHEL, CentOS, and Ubuntu, with Oracle Linux, CentOS, SUSE, and Debian being added shortly. In addition, TVM now also provides secure configuration assessment capabilities for Linux and macOS. These allow organizations to discover, prioritize, and remediate dozens of insecure configurations to improve their overall security posture.
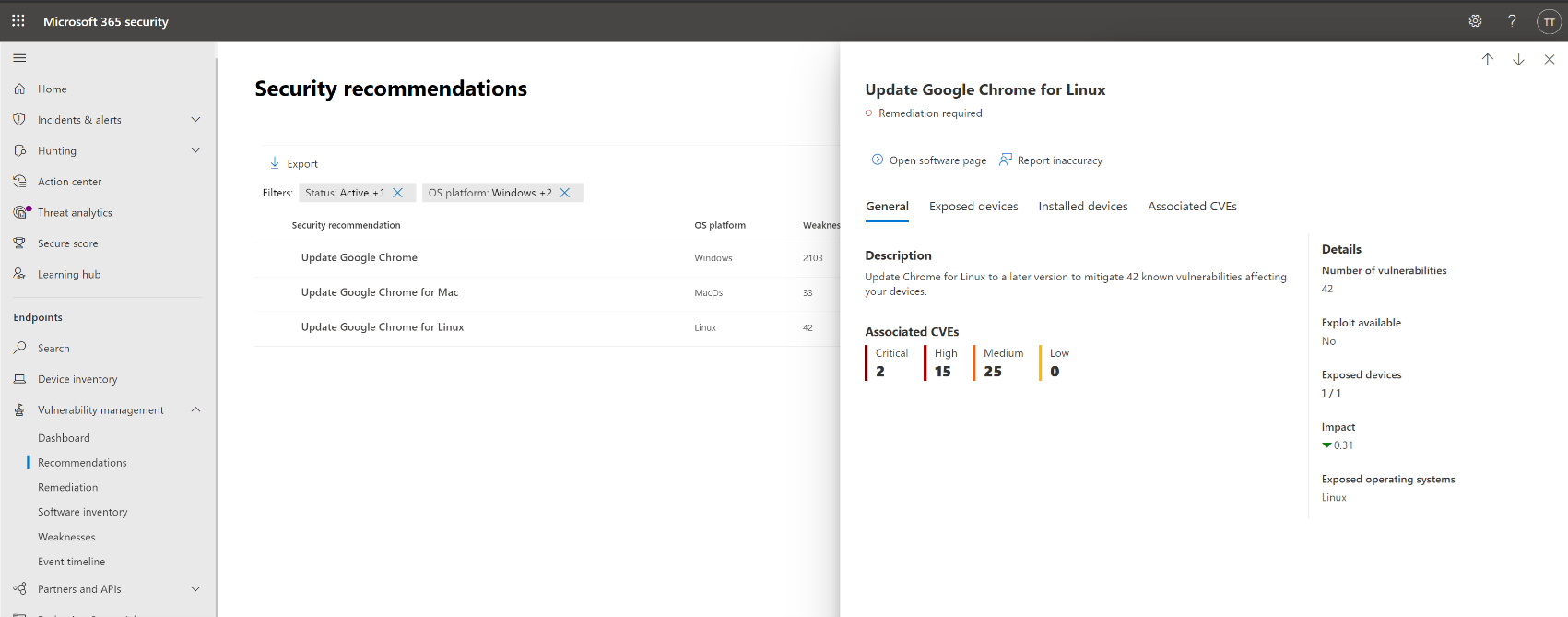
Figure 1: Security recommendation to update Google Chrome for Windows, macOS, and Linux.

Figure 2: Details of all vulnerabilities associated with Google Chrome for Linux.
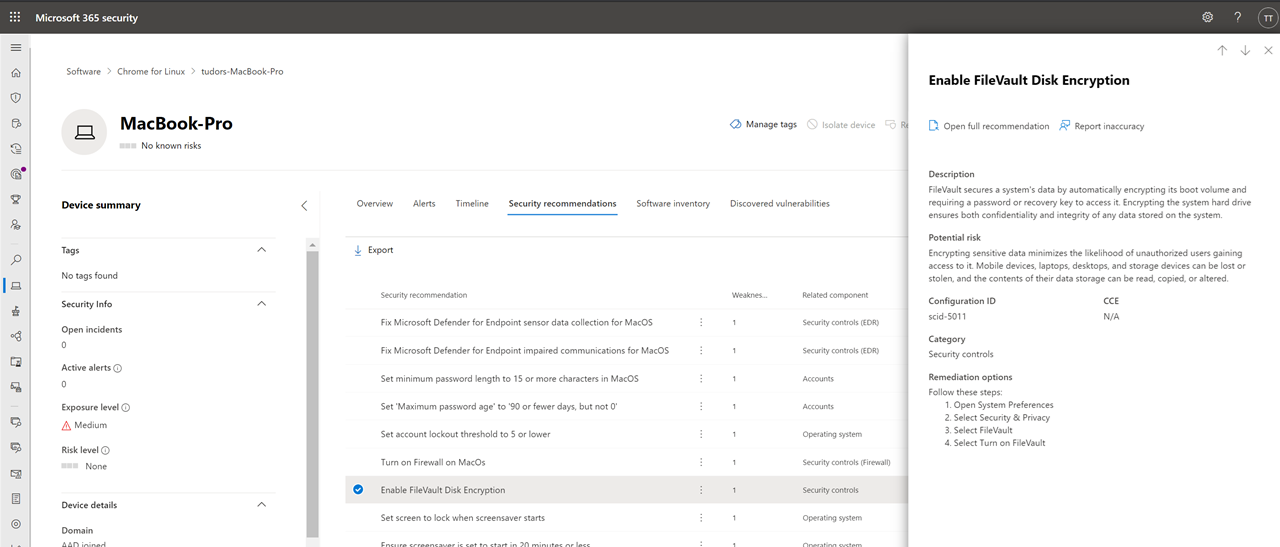
Figure 3: Security configuration recommendation for macOS.
Microsoft’s investment in cross-platform coverage now enables customers to take full advantage of the powerful TVM capabilities on all major platforms across managed and unmanaged devices. They are available in Microsoft Defender for Endpoint as part of an integrated experience that provides device context, prioritizes based on risk, and minimizes time to remediation across their entire portfolio of managed and unmanaged devices.
An added focus on interoperability
As we continue to expand the coverage for our TVM capabilities and remain focused on providing natively integrated experiences across the Microsoft portfolio, we are also partnering with industry-leading solution providers to ensure the interoperability of our solution.
We understand that our customers have existing investments and established processes to run their security and IT operations. That is why a broad ecosystem of integration partners is a critical focus as we continue to grow our vulnerability management capabilities. Customers can already leverage integrations with Skybox, Kenna Security, and ServiceNow Vulnerability Response, and we are actively working on expanding this list.
In addition, the Threat and vulnerability management APIs give customers and partners full access to the threat and vulnerability management dataset, including vulnerability assessment, security configuration assessment, and the software inventory for all devices. This enables any partner to leverage and integrate threat and vulnerability management data into their platforms and create custom solutions with the available data set.
As a hybrid workforce becomes the new normal and organizations continue to face new security challenges, Microsoft Threat and Vulnerability Management enables better insight into organizational risk and the overall security posture of their devices. With a focus on broad platform support and interoperability, we are committed to providing customers with the flexibility and coverage they need to detect vulnerabilities and misconfigurations early on and make remediation simple.
Learn more
Microsoft Threat and Vulnerability Management bridges the gap between security and IT teams to seamlessly remediate vulnerabilities and reduce risk in your organization. It is deeply integrated with Microsoft’s portfolio of security and IT management solutions, and you can sign up for a free trial today or get started even faster with our interactive guide.
To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.








