Cybersecurity jobs are more challenging than ever. It’s not just increased speed, scale, and sophistication of cyberattacks that make cybersecurity jobs harder: there are 250 new regulatory updates to be tracked every day,1 cybersecurity teams have a disconnected collection of fragmented tools that they are expected to seamlessly stitch together and manage, and the cybersecurity workforce gap has reached a record high, with 4 million professionals needed to adequately secure organizations.2 Still, security is the most important investment we can make, especially as AI reshapes the world.
In response, many leading organizations are re-evaluating their security strategy and moving away from a patchwork of disparate solutions in an effort to reduce costs, eliminate gaps, and improve security posture overall. They are adopting an end-to-end security approach, which is not an entirely new concept but rather an evolving vision of the technology, culture, and training necessary to tackle cybersecurity successfully. End-to-end security focuses on fully securing your entire digital estate pre- and post-breach, with management, mitigation, and assessment capabilities. For instance, Microsoft Security spans more than 50 categories within six product families, aligning seamlessly with our Security Future Initiative efforts introduced in November 2023.
End-to-end security is a comprehensive and proactive approach to protecting your environment that is grounded in a Zero Trust security strategy. It’s about a cohesive user experience as much as it is about complete threat intelligence and a consistent data platform. All products work together effectively to address identity, devices, clouds, data, and network. It requires that you have a multitude of capabilities in place, from identity to data to threat protection to governance and compliance. It protects you from every angle, across security, compliance, identity, device management, and privacy. And you can accelerate the benefits of end-to-end security even further with generative AI.
Zero Trust security
Build a secure hybrid workforce and drive business agility with a Zero Trust approach to security.

Why an evolving landscape makes end-to-end security appealing
You can’t protect what you can’t see or understand. Many organizations are siloed rather than possessing a single vision for cybersecurity. And when these siloed areas of the organization—perhaps none are more siloed than IT and security teams—are not talking to each other, the integration of tools, people, and processes faces a major roadblock. With AI tools gaining popularity in the digital workplace, communication challenges are more apparent as organizations seek increased visibility and greater control of AI usage.
Another challenge is the enormous scale of data that needs analysis to produce threat intelligence and effective threat response. The volume can be overwhelming, and with a patchwork security strategy, even best-in-breed tools are less effective because they cannot contribute to a complete view of the data and offer no way to organize it.
To optimize for the evolving landscape, organizations are changing their security priorities.
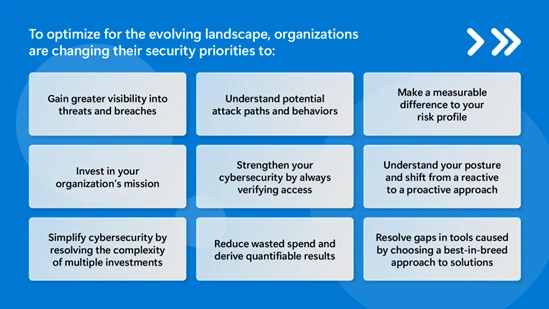
Figure 1. A list of nine of the top security priorities organizations should implement in the face of the ever evolving cybersecurity landscape.
The desire for simplification and more effective security are motivating organizations to move to an end-to-end security approach because of significant advantages. Microsoft customers tell us that juggling myriad security products is difficult to maintain and they want to seize opportunities for AI and better manage risk.
ING, one of the biggest banks in Europe, is a great example of how an organization benefits from an end-to-end approach. ING consolidated a fragmented, complicated mix of security tools into an end-to-end security approach for better protection of their private, public, and multicloud environments. The firm is using the solution to protect the company and the 38 million customers it serves across 40 countries.
What are the advantages of an end-to-end security approach?
The end-to-end security approach consolidates all your cybersecurity tools, from data protection to incident response and everything in between, into one solution. According to IDC’s North American Tools and Vendors Consolidation Survey conducted in November and December 2023, approximately 86% of organizations are either actively consolidating or planning to consolidate their tools. And 50% of those planning a consolidation have almost 50 tools (20 vendors on average).3 By interconnecting different tools through APIs, you simplify the security of your organization and gain greater visibility over everything happening. Without that visibility, you lack the knowledge of what you need to protect and govern your data, as well as investigate when a breach occurs.
When combined with AI, end-to-end security overcomes challenges that can’t be solved by automation or code. That kind of agility is critical to address potential risks and successfully defend against modern cyberthreats, especially in confronting the scale at which breaches are occurring.
Plus, end-to-end security solves challenges in a way that allows for data gravity, which involves bringing applications and services to your data rather than the other way around. It’s useful in instances where the data is extremely large. Introducing data gravity enables new types of security scenarios to be built, sparking innovation in your security strategy. And end-to-end security paves the way for security assessments of your resources and other benefits of continuous posture management.
“By adopting multiple interoperable Microsoft security solutions, we have improved our preventative capabilities, our incident response times, and our scope for monitoring our environment,” said Glauco Sampaio, Chief Information Security Officer at Cielo. “It was surprisingly simple to enable real-time visibility across our environment. It’s been a leap in our security maturity level.”
Explore how adopting end-to-end security benefits you
Taking an end-to-end approach to security can pay major dividends, especially as you align to the Zero Trust framework. You will be able to determine which solutions to deploy and identify any gaps. An end-to-end approach will help you consolidate the number of tools and applications and use the ones that maximize your benefits. To explore how Microsoft Security with Microsoft Copilot for Security enables you to safeguard your people, data, and infrastructure, visit our webpage.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
1Microsoft Execs: Partners ‘Critical’ To Achieving Responsible AI, Security, CRN. May 23, 2024.
2ISC2 Publishes 2023 Workforce Study, ISC2. October 31, 2023.
3North American Security Tools and Vendors Consolidation Study: Insights on Product Consolidation Plans, IDC. April 2024.








