As the agentic era reshapes security operations, leaders face a strategic inflection point: legacy security information and event management (SIEM) solutions and fragmented toolchains can no longer keep pace with the scale, speed, and complexity of modern cyberthreats. Organizations can choose to spend the next year tuning and integrating their SIEM stack—or simplify the architecture and let a unified platform do the heavy lifting. If they choose a platform, it should make it inexpensive to ingest and retain more telemetry, automatically shape that data into analysis‑ready form, and enrich it with graph‑driven intelligence so both analysts and AI can quickly understand what matters and why. The strategic SIEM buyer’s guide outlines what decision‑makers should look for as they build a future‑ready security operations center (SOC). Read on for a preview of key concepts covered in the guide.
Build a unified, future-proof foundation
As organizations step into the agentic AI era, the priority shifts to establishing a security foundation that can absorb rapid change without adding operational drag. That requires an architecture built for flexibility—one that brings security data, analytics, and response capabilities together rather than scattering them across aging infrastructure. A unified, cloud‑native platform gives security teams the structural advantage of consistent visibility, elastic scale, and a single source of truth for both human analysts and AI systems. By consolidating core functions into one environment, leaders can modernize the SOC in a deliberate, sustainable way while positioning their teams to capitalize on emerging AI‑powered security capabilities.
Accelerate detection and response with AI
As cyberthreats evolve faster than traditional workflows can manage, the advantage shifts to SOCs that can elevate detection and response with adaptive automation. Modern platforms augment analysts with real‑time correlation, automated investigation, and adaptive orchestration that reduces manual steps and shortens exposure windows. By standardizing access to high‑quality security data and enabling agents to act on that context, organizations improve precision, reduce noise, and transition from reactive triage to continuous, intelligence‑driven response. This shift not only accelerates outcomes but frees teams to focus on higher‑value threat hunting and strategic risk reduction.
Maximize return on investment and accelerate time to value
Driving measurable value is now a leadership imperative, and modern SIEM platforms must deliver results without protracted deployments or heavy reliance on specialized expertise. AI-ready solutions reduce onboarding friction through prebuilt connectors, embedded analytics, and turnkey content that produce meaningful detection coverage within hours—not months.
“Microsoft Sentinel’s ease of use means we can go ahead and deploy our solutions much faster. It means we can get insights into how things are operating more quickly.”
—Director of IT in the healthcare industry
By consolidating core workflows into a single environment, organizations avoid the hidden costs of operating multiple tools and shorten the path from implementation to impact. As adaptive AI optimizes configurations, prioritizes coverage gaps, and streamlines operations, security leaders gain a clearer return on investment while reallocating resources toward strategic risk reduction instead of maintenance and integration work. AI‑ready solutions reduce onboarding friction through pre‑built connectors, embedded analytics, and turnkey content that produce meaningful detection coverage within hours—not months.
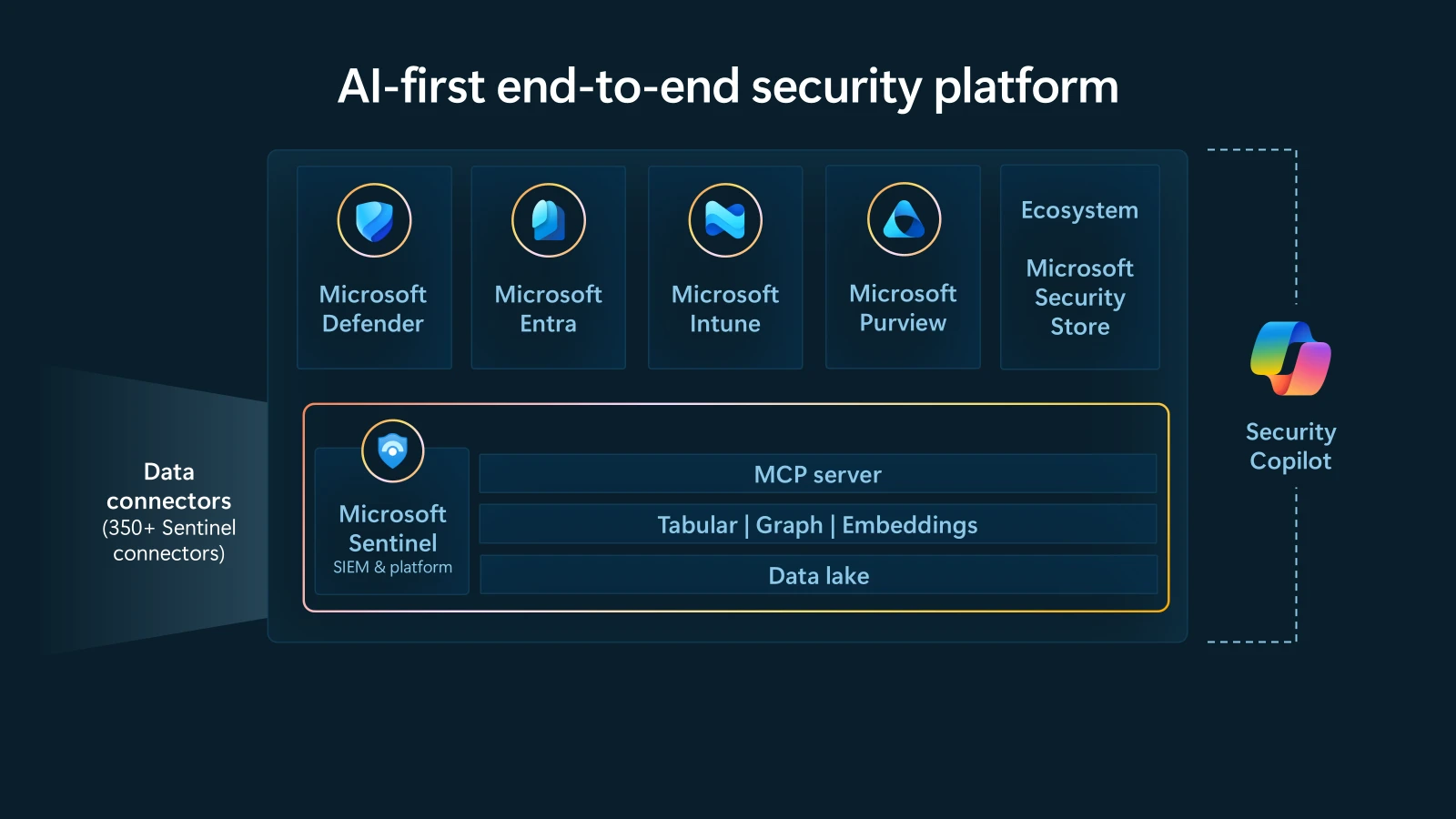
Turning guidance into action with Microsoft
The guide also outlines where Microsoft Sentinel delivers meaningful advantages for modern SOC leaders—from its cloud‑native scale and unified data foundation to integrated SIEM, security orchestration, automation, and response (SOAR), extended detection and response (XDR), and advanced analytics in a single AI‑ready platform. It includes practical tips for evaluating vendors, highlighting the importance of unification, cloud‑native elasticity, and avoiding fragmented add‑ons that drive hidden costs. Together, the three essentials—building a unified foundation, accelerating detection and response with AI, and maximizing return on investment through rapid time to value—establish a clear roadmap for modernizing security operations.
Read The strategic SIEM buyer’s guide for the full analysis, vendor considerations, and detailed guidance on selecting an AI‑ready platform for the agentic era.
Learn more
Learn more about Microsoft Sentinel or discover more about Microsoft Unified SecOps.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.








