

Threat intelligence
The Microsoft Threat Intelligence community is made up of world-class experts, security researchers, analysts, and threat hunters who analyze 100 trillion signals daily to discover threats and deliver timely and timely, relevant insight to protect customers. See our latest findings, insights, and guidance.
Refine results
Topic
Products and services
Publish date
-
There are tools available that can ease kick-off activities for CISOs, CIOs, and DPOs.
-
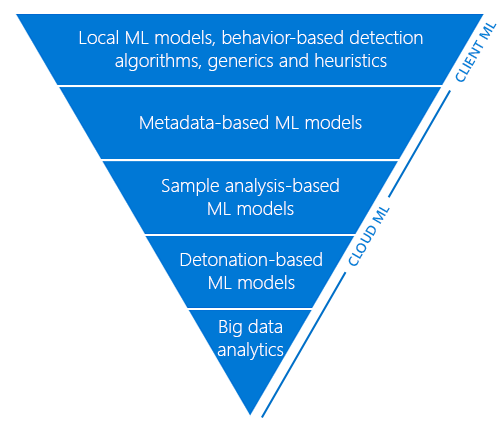
Detonating a bad rabbit: Windows Defender Antivirus and layered machine learning defenses
Windows Defender Antivirus uses a layered approach to protection: tiers of advanced automation and machine learning models evaluate files in order to reach a verdict on suspected malware. -
Office 365 Advanced Threat Protection defense for corporate networks against recent Office exploit attacks
The Office 365 Threat Research team has seen an uptick in the use of Office exploits in attacks across various industry sectors in recent months. -
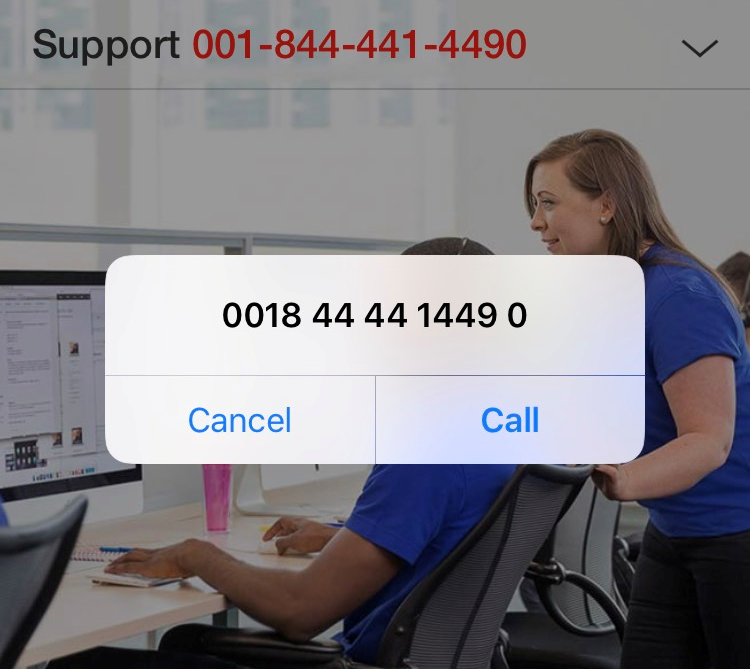
New tech support scam launches communication or phone call app
(Note: Our Tech support scams FAQ page has the latest info on this type of threat, including scammer tactics, fake error messages, and the latest scammer hotlines. -
#AVGater vulnerability does not affect Windows Defender Antivirus, MSE, or SCEP
On November 10, 2017, a vulnerability called #AVGater was discovered affecting some antivirus products. -
Introducing Windows Defender Application Control
Application control is a crucial line of defense for protecting enterprises given today’s threat landscape, and it has an inherent advantage over traditional antivirus solutions. -
Microsoft to remove WoSign and StartCom certificates in Windows 10
Microsoft has concluded that the Chinese Certificate Authorities (CAs) WoSign and StartCom have failed to maintain the standards required by our Trusted Root Program. -
Windows Defender ATP machine learning: Detecting new and unusual breach activity
Microsoft has been investing heavily in next-generation security technologies. -
TLS 1.2 Support added to Windows Server 2008
We are announcing that support for TLS1. -
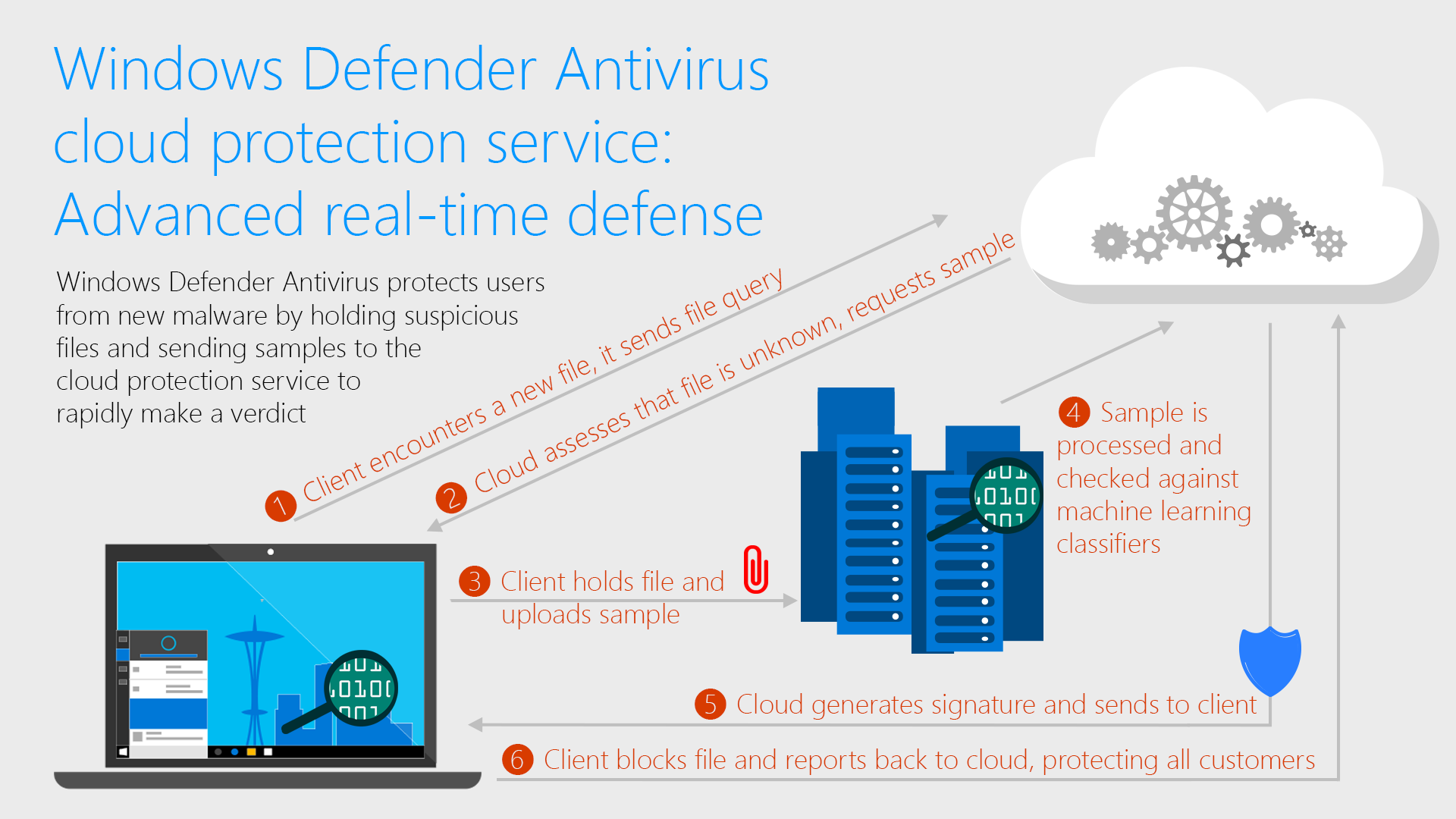
Windows Defender Antivirus cloud protection service: Advanced real-time defense against never-before-seen malware
For cybercriminals, speed is the name of the game. -
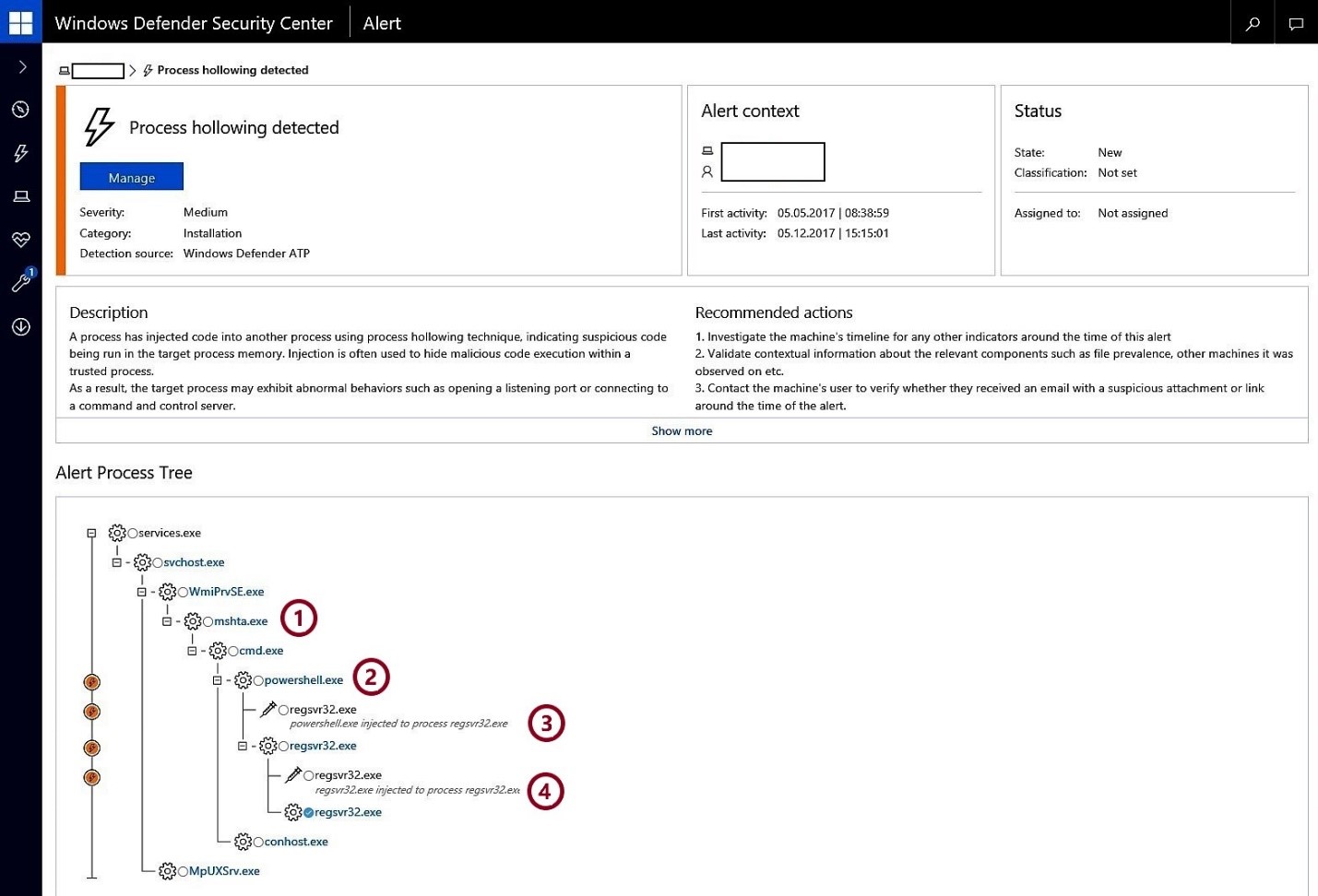
Detecting stealthier cross-process injection techniques with Windows Defender ATP: Process hollowing and atom bombing
Advanced cyberattacks emphasize stealth and persistence: the longer they stay under the radar, the more they can move laterally, exfiltrate data, and cause damage.





