Strengthen your Zero Trust posture—a new, unified approach to security is here
Embrace proactive security with Zero Trust
Accelerate your Zero Trust implementation with best practices, the latest trends, and a framework informed by real-world deployments.
Why Zero Trust
Today’s organizations need a new security model that more effectively adapts to the complexity of the modern environment, embraces the hybrid workplace, and protects people, devices, apps, and data wherever they’re located.
Productivity everywhere
Empower your users to work more securely anywhere and anytime, on any device.
Cloud migration
Enable digital transformation with intelligent security for today’s complex environment.
Risk mitigation
Close security gaps and minimize risk of lateral movement.
Zero Trust principles
Verify explicitly
Always authenticate and authorize based on all available data points, including user identity, location, device health, service or workload, data classification, and anomalies.
Use least-privilege access
Limit user access with just-in-time (JIT) and just-enough access (JEA), risk-based adaptive polices, and data protection to help secure both data and productivity.
Assume breach
Minimize blast radius and segment access. Verify end-to-end encryption and use analytics to get visibility, drive threat detection, and improve defenses.
Build a secure hybrid workforce
Drive business agility with a Zero Trust approach to security.

Securely work from anywhere
Enhance the employee experience with adaptable security policies that help you effectively manage and protect all your devices and identities, no matter where people choose to work.

Safeguard your most critical assets
Secure your data even as it moves beyond your network with unified data protection and governance best practices.

Modernize your security posture
Reduce security vulnerabilities with expanded visibility across your digital environment, risk-based access controls, and automated policies.

Minimize the impact of bad actors
Safeguard your organization from both internal and external risks with a layered defense that explicitly verifies all access requests.

Get ahead of regulatory requirements
Keep up with the evolving compliance landscape with a comprehensive strategy that helps you seamlessly protect, manage, and govern your data.
What’s next in your Zero Trust journey?
Assess the Zero Trust maturity stage of your organization and receive targeted milestone guidance, plus a curated list of resources and solutions to move forward in your comprehensive security posture.

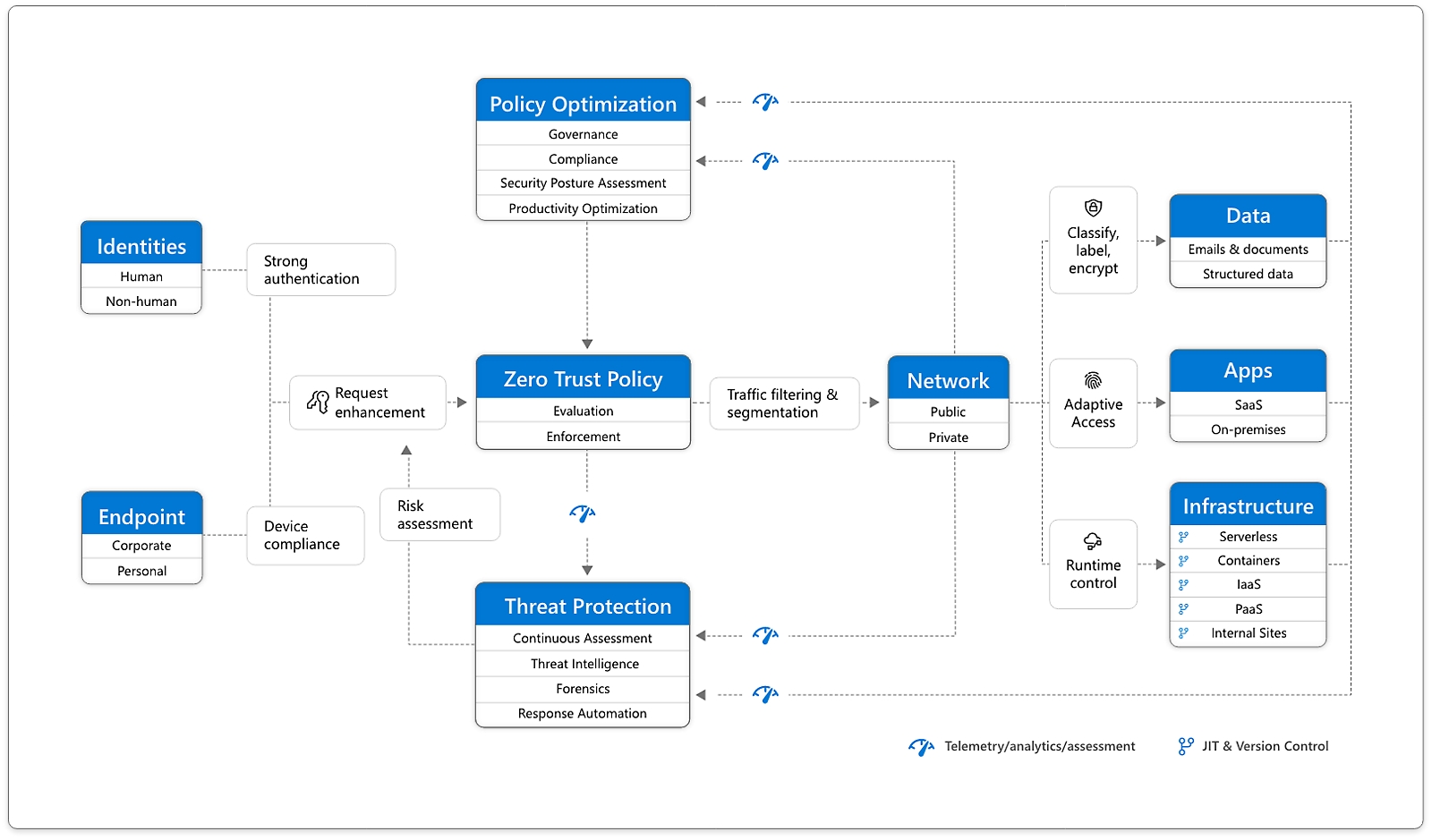
Zero Trust defined
Instead of assuming everything behind the corporate firewall is safe, the Zero Trust model assumes breach and verifies each request as though it originates from an open network. Regardless of where the request originates or what resource it accesses, Zero Trust teaches us to “never trust, always verify.” Every access request is fully authenticated, authorized, and encrypted before granting access. Microsegmentation and least-privilege access principles are applied to minimize lateral movement. Rich intelligence and analytics are utilized to detect and respond to anomalies in real time.
Zero Trust defense areas

Identities
Verify and secure each identity with strong authentication across your entire digital estate.

Endpoints
Gain visibility into devices accessing the network. Ensure compliance and health status before granting access.

Apps
Discover shadow IT, ensure appropriate in-app permissions, gate access based on real-time analytics, and monitor and control user actions.

Data
Move from perimeter-based data protection to data-driven protection. Use intelligence to classify and label data. Encrypt and restrict access based on organizational policies.

Infrastructure
Use telemetry to detect attacks and anomalies, automatically block and flag risky behavior, and employ least-privilege access principles.

Network
Ensure that devices and users aren’t trusted just because they’re on an internal network. Encrypt all internal communications, limit access by policy, and employ microsegmentation and real-time threat detection.
Demos and expert insights
Episode 1: Zero Trust Essentials
Learn about Zero Trust, the six areas of defense, and how Microsoft products can help in the first episode of Microsoft Mechanics’ Zero Trust Essentials series with host Jeremy Chapman.
Episode 2: Identity Controls
Get tips and watch demos of the tools for implementing the Zero Trust security model for identity and access management.
Episode 3: Endpoints and Applications
Learn more about defending endpoints and apps with Zero Trust, including product demonstrations from Microsoft.
Episode 4: Network and Infrastructure
Host Jeremy Chapman explains how to apply Zero Trust principles to your network and infrastructure using Microsoft Azure.
Episode 5: Data
Protect data across your files and content - in transit, in use and wherever it resides - with the Zero Trust security model.
Discover how customers are making Zero Trust a reality
Inform your strategy and adoption

Implementing Zero Trust at Microsoft
Microsoft has adopted a Zero Trust strategy to secure corporate and customer data. The implementation centers on strong user identity, device health verification, validation of app health, and least-privilege access to resources and services.

Deploy, integrate, and develop
Take the next steps in your organization’s end-to-end implementation. with ourGo to the Zero Trust Guidance Center docs for deployment, integration, and app development documentation and best practices.

Compare your progress
Get the latest research on how and why organizations are adopting Zero Trust to help inform your strategy, uncover collective progress and prioritizations, and gain insights on this rapidly evolving space.
More resources
Zero Trust security blogs
Learn about the latest trends in Zero Trust in cybersecurity from Microsoft.
Microsoft Security Blog
Discover successful security strategies and valuable lessons learned from top experts.
US Executive Order
Explore resources for federal agencies to improve national cybersecurity through cloud adoption and Zero Trust.
Security Partners
Browse solution providers and independent software vendors to help you bring Zero Trust to life.
Frequently asked questions
-
Zero Trust is a modern security strategy based on the principle never trust, always verify. Instead of assuming everything behind the corporate firewall is safe, the Zero Trust model assumes breach and verifies each request as though it originates from an open network.
-
The three main pillars of Zero Trust are:
- Verify explicitly: always authenticate and authorize based on all available data points, including user identity, location, device health, service or workload, data classification, and anomalies.
- Use least-privilege access: limit user access with just-in-time and just-enough-access, risk-based adaptive polices, and data protection to help secure data and improve productivity.
- Assume breach: verify end-to-end encryption and use analytics to gain visibility, detect threats, and improve defenses.
-
Organizations need Zero Trust solutions because security has become more complex. As increasing numbers of employees work remotely, it’s no longer sufficient to just protect the network perimeter. Organizations need adaptive solutions that fully authenticate and verify every access request and quickly detect and respond to threats both inside and outside the network.
-
Zero Trust helps solve the problem of greater complexity. Today’s organizations need to protect a growing volume of data across a multiplatform, multicloud environment. Risks to that data have increased as more companies turn to hybrid work and attacks become more sophisticated. Zero Trust helps simplify security with a strategy, processes, and automated tools that verify every transaction, enforce least-privilege access, and apply advanced detection and response to threats.
-
A Zero Trust network fully authenticates, authorizes, and encrypts every access request, applies microsegmentation and least-privilege access principles to minimize lateral movement, and uses intelligence and analytics to detect and respond to anomalies in real time.
-
One of the most effective Zero Trust policies is multifactor authentication. Requiring that every user perform two or more forms of authentication (such as using a PIN on a known device) every time they sign in significantly decreases the risk that a bad actor with stolen credentials will gain access.
-
Implementing a Zero Trust strategy starts with identifying business priorities and gaining leadership buy-in. It may take many years to complete the rollout, so it helps to start with easy wins and prioritize tasks based on business goals. An implementation plan will typically include the following steps:
- Roll out identity and device protection, including multifactor authentication, least-privilege access, and conditional access policies.
- Enroll endpoints in a device-management solution to ensure devices and apps are up to date and meet organizational requirements.
- Deploy an extended detection and response solution to detect, investigate, and respond to threats across endpoints, identities, cloud apps, and emails.
- Protect and govern sensitive data with solutions that provide visibility into all data and apply data loss prevention policies.
Go to the Zero Trust Guidance Center for additional resources.
-
SASE is a security framework that combines software-defined wide area networking (SD-WAN) and Zero Trust security solutions into a converged cloud-delivered platform that securely connects users, systems, endpoints, and remote networks to apps and resources.
Zero Trust, which is a modern security strategy that centers on verifying each access request as though it originates from an open network, is one component of SASE. SASE also includes SD-WAN, Secure web gateway, cloud access security broker, and firewall as a service, all centrally managed through a single platform.
-
A VPN is a technology that enables remote employees to connect to the corporate network.
Zero Trust is a high-level strategy that assumes that individuals, devices, and services that are attempting to access company resources, even those inside the network, cannot automatically be trusted. To enhance security these users are verified every time they request access, even if they were authenticated earlier.


Follow Microsoft