Microsoft Security Blog
Your source for the latest in cybersecurity
Secure agentic AI for your Frontier Transformation
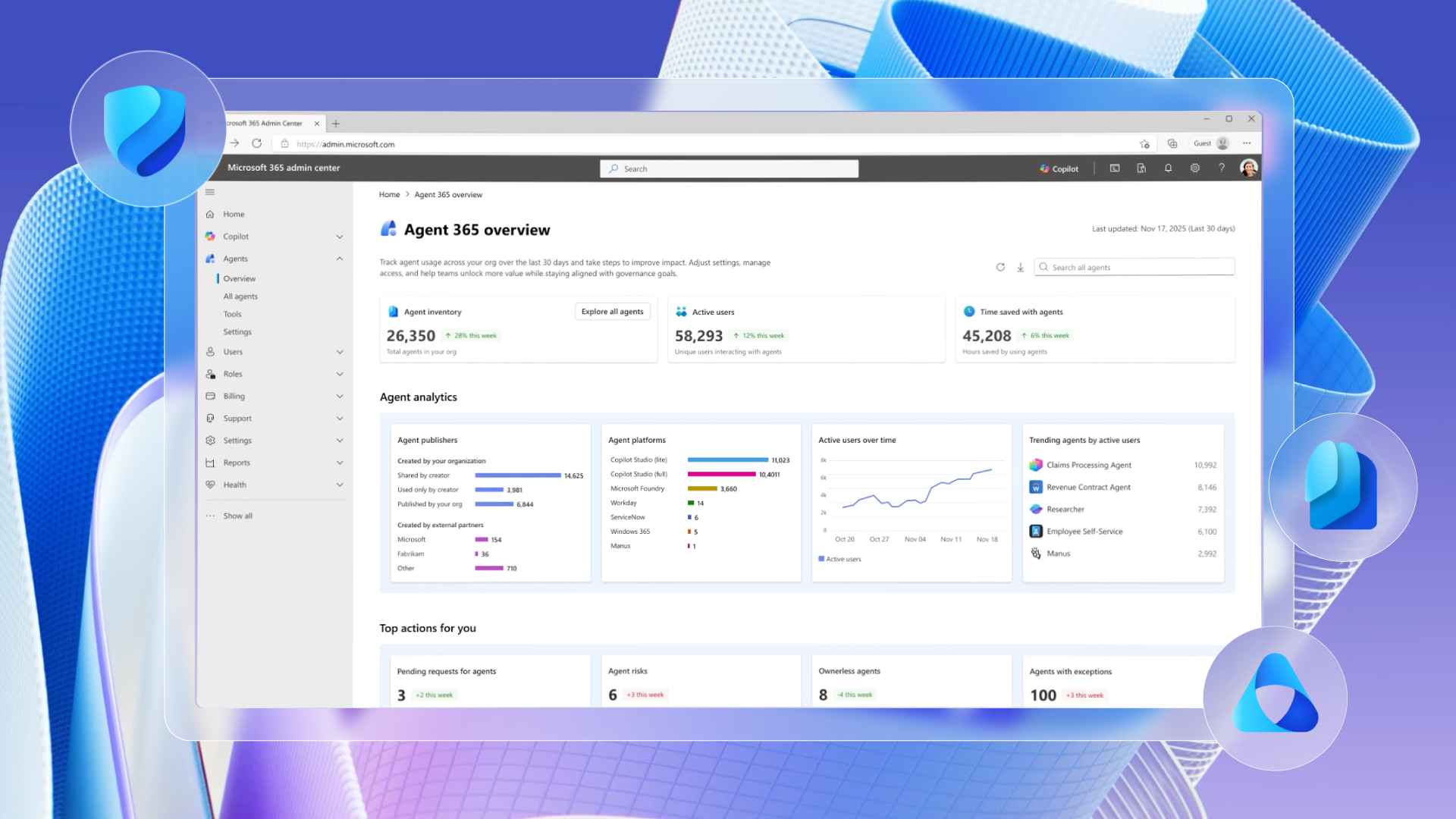
We are announcing the next step to make Frontier Transformation real for customers across every industry with Wave 3 of Microsoft 365 Copilot, Microsoft Agent 365, and Microsoft 365 E7: The Frontier Suite.

Women’s History Month: Encouraging women in cybersecurity at every career stage
This Women’s History Month, we explore ways to support the next generation of female defenders at every career stage.

When tax season becomes cyberattack season: Phishing and malware campaigns using tax-related lures
During tax season, threat actors reliably take advantage of the urgency and familiarity of time-sensitive emails, including refund notices, payroll forms, filing reminders, and requests from tax professionals, to push malicious attachments, links, or QR codes.
Stay ahead of threats
Get expert insights, threat intelligence, and the latest cybersecurity reports from Security Insider.
AI and machine learning
-

Addressing the OWASP Top 10 Risks in Agentic AI with Microsoft Copilot Studio
Agentic AI introduces new security risks. -

Identity security is the new pressure point for modern cyberattacks
Read the latest Microsoft Secure Access report for insights into why a unified identity and access strategy offers strong modern protection. -
Governing AI agent behavior: Aligning user, developer, role, and organizational intent
This research report explores the layers of agent intent and how to align them for secure enterprise AI adoption.
Modernize your security operations center
Confidently secure your multicloud, multiplatform environment with Microsoft Sentinel – a cloud-native security information and event management (SIEM) solution.
Latest posts
-

Addressing the OWASP Top 10 Risks in Agentic AI with Microsoft Copilot Studio
Agentic AI introduces new security risks. -

Identity security is the new pressure point for modern cyberattacks
Read the latest Microsoft Secure Access report for insights into why a unified identity and access strategy offers strong modern protection. -

Guidance for detecting, investigating, and defending against the Trivy supply chain compromise
Threat actors abused trusted Trivy distribution channels to inject credential‑stealing malware into CI/CD pipelines worldwide. -
Governing AI agent behavior: Aligning user, developer, role, and organizational intent
This research report explores the layers of agent intent and how to align them for secure enterprise AI adoption.





