Researchers at the Eindhoven University of Technology recently revealed information around “Thunderspy,” an attack that relies on leveraging direct memory access (DMA) functionality to compromise devices. An attacker with physical access to a system can use Thunderspy to read and copy data even from systems that have encryption with password protection enabled.
Secured-core PCs provide customers with Windows 10 systems that come configured from OEMs with a set of hardware, firmware, and OS features enabled by default, mitigating Thunderspy and any similar attacks that rely on malicious DMA.
How Thunderspy works
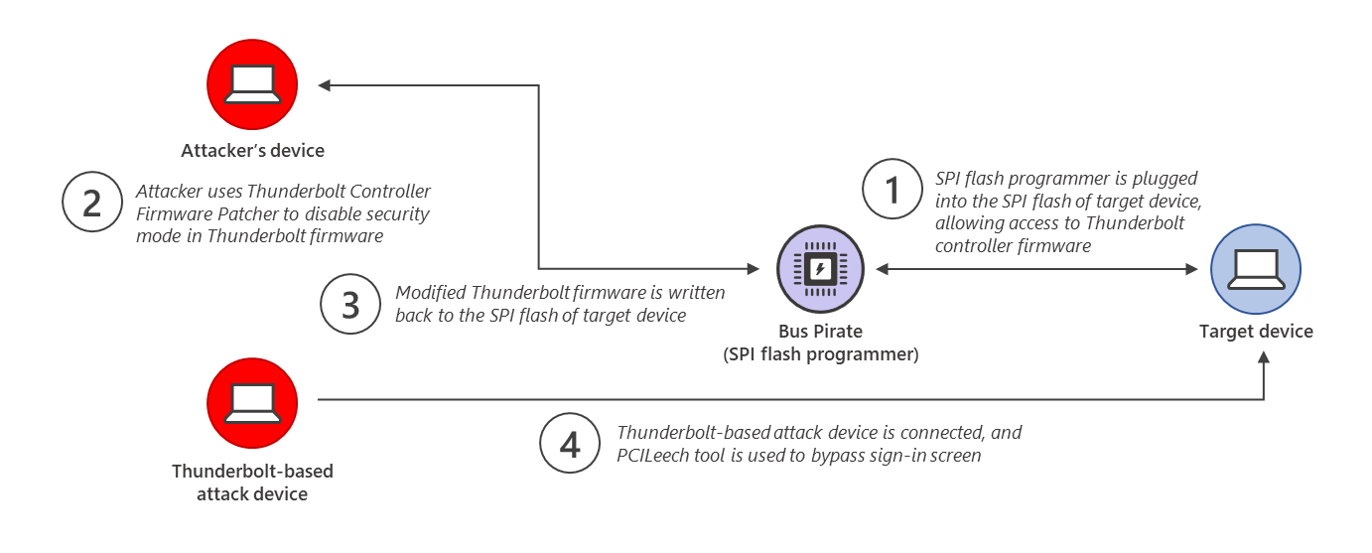
Like any other modern attack, Thunderspy relies on not one but multiple building blocks being chained together. Below is a summary of how Thunderspy can be used to access a system where the attacker does not have the password needed to sign in. A video from the Thunderspy research team showing the attack is available here.
Step 1: A serial peripheral interface (SPI) flash programmer called Bus Pirate is plugged into the SPI flash of the device being attacked. This gives access to the Thunderbolt controller firmware and allows an attacker to copy it over to the attacker’s device
Step 2: The Thunderbolt Controller Firmware Patcher (tcfp), which is developed as part of Thunderspy, is used to disable the security mode enforced in the Thunderbolt firmware copied over using the Bus Pirate device in Step 1
Step 3: The modified insecure Thunderbolt firmware is written back to the SPI flash of the device being attacked
Step 4: A Thunderbolt-based attack device is connected to the device being attacked, leveraging the PCILeech tool to load a kernel module that bypasses the Windows sign-in screen
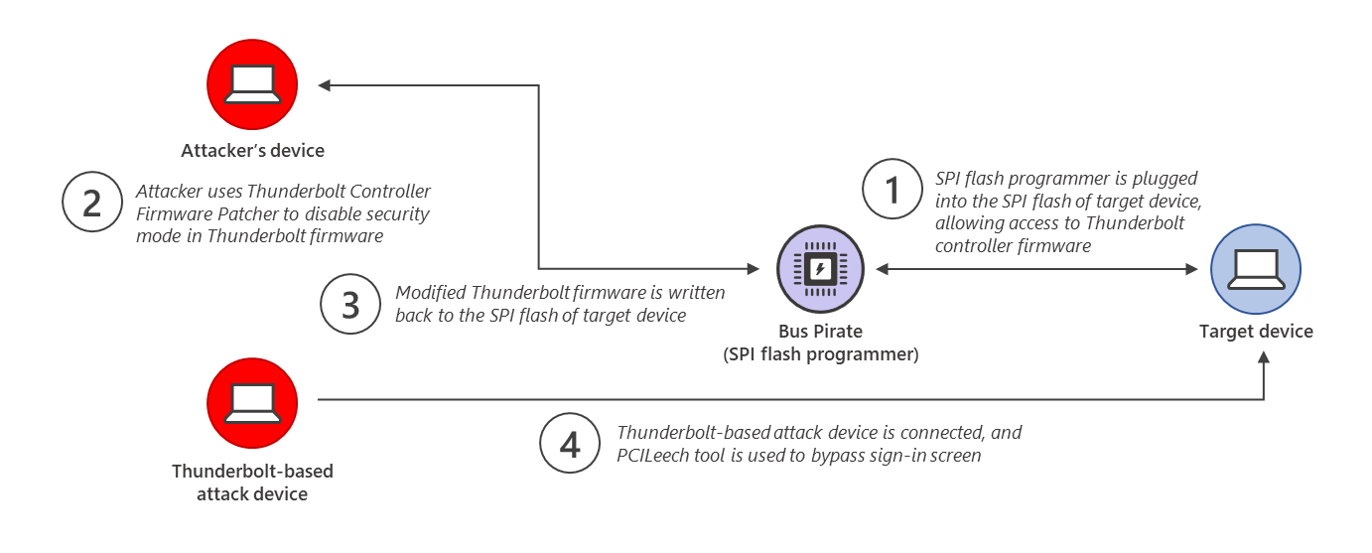
The result is that an attacker can access a device without knowing the sign-in password for the device. This means that even if a device was powered off or locked by the user, someone that could get physical access to the device in the time it takes to run the Thunderspy process could sign in and exfiltrate data from the system or install malicious software.
Secured-core PC protections
In order to counteract these targeted, modern attacks, Secured-core PCs use a defense-in-depth strategy that leverage features like Windows Defender System Guard and virtualization-based security (VBS) to mitigate risk across multiple areas, delivering comprehensive protection against attacks like Thunderspy.
Mitigating Steps 1 to 4 of the Thunderspy attack with Kernel DMA protection
Secured-core PCs ship with hardware and firmware that support Kernel DMA protection, which is enabled by default in the Windows OS. Kernel DMA protection relies on the Input/Output Memory Management Unit (IOMMU) to block external peripherals from starting and performing DMA unless an authorized user is signed in and the screen is unlocked. Watch this video from the 2019 Microsoft Ignite to see how Windows mitigates DMA attacks.
This means that even if an attacker was able to copy a malicious Thunderbolt firmware to a device, the Kernel DMA protection on a Secured-core PC would prevent any accesses over the Thunderbolt port unless the attacker gains the user’s password in addition to being in physical possession of the device, significantly raising the degree of difficulty for the attacker.
Hardening protection for Step 4 with Hypervisor-protected code integrity (HVCI)
Secured-core PCs ship with hypervisor protected code integrity (HVCI) enabled by default. HVCI utilizes the hypervisor to enable VBS and isolate the code integrity subsystem that verifies that all kernel code in Windows is signed from the normal kernel. In addition to isolating the checks, HVCI also ensures that kernel code cannot be both writable and executable, ensuring that unverified code does not execute.
HVCI helps to ensure that malicious kernel modules like the one used in Step 4 of the Thunderspy attack cannot execute easily as the kernel module would need to be validly signed, not revoked, and not rely on overwriting executable kernel code.
Modern hardware to combat modern threats
A growing portfolio of Secured-core PC devices from the Windows OEM ecosystem are available for customers. They provide a consistent guarantee against modern threats like Thunderspy with the variety of choices that customers expect to choose from when acquiring Windows hardware. You can learn more here: https://www.microsoft.com/en-us/windowsforbusiness/windows10-secured-core-computers
Nazmus Sakib
Enterprise and OS Security