Patch me if you can: Cyberattack Series
The Microsoft Incident Response team takes swift action to help contain a ransomware attack and regain positive administrative control of the customer environment.

Instead of believing everything behind the corporate firewall is safe, the Zero Trust model assumes breach and verifies each request as though it originates from an uncontrolled network. Regardless of where the request originates or what resource it accesses, Zero Trust teaches us to “never trust, always verify.”
At Microsoft, we consider Zero Trust an essential component of any organization’s security plan based on these three principles:
In this article, we will focus on the third principle (assume breach) and how encryption and data protection play a significant role in getting prepared for a potential breach in your data center.
As part of a comprehensive security posture, data should always be encrypted so that in the event where an attacker is able to intercept customer data, they are unable to decipher usable information.
End-to-end encryption is applied throughout the following three stages: at rest, in transit, and in use.
Data protection is critical across all three of these stages, so let’s dive a little deeper into how each stage works and how it can be implemented.
Encryption at rest provides data protection for stored data (at rest). Attacks against data at rest include attempts to obtain physical access to the hardware on which the data is stored, and then compromising the contained data. In such an attack, a server’s hard drive may have been mishandled during maintenance allowing an attacker to remove the hard drive. Later the attacker would put the hard drive into a computer under their control to attempt to access the data.
Encryption at rest is designed to prevent the attacker from accessing the unencrypted data by ensuring the data is encrypted when on disk. If an attacker obtains a hard drive with encrypted data but not the encryption keys, the attacker must defeat the encryption to read the data. This attack is much more complex and resource-consuming than accessing unencrypted data on a hard drive. For this reason, encryption at rest is highly recommended and is a high priority requirement for many organizations.
At rest, it is important that your data is protected through disk encryption which enables IT administrators to encrypt your entire virtual machine (VM) or operating system (OS) disks.
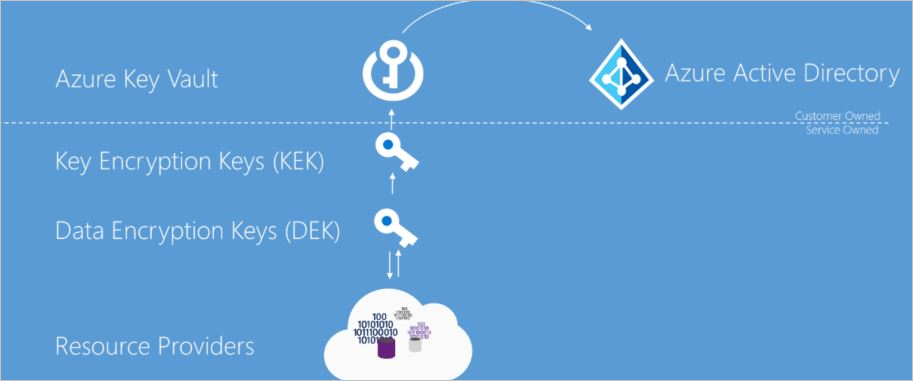
One of the concerns that we hear from customers is how can they reduce the chances that certificates, passwords, and other secrets may accidentally get leaked. A best practice is to use central storage of application secrets in a secured vault to have full control of their distribution. When using a secured vault, application developers no longer need to store security information in their applications, which reduces risk by eliminating the need to make this information part of the code.
Data encryption at rest is a mandatory step toward data privacy, compliance, and data sovereignty. These Microsoft Azure security services are recommended for this purpose:
A “data in transit” condition exists when data is transferred within the data center between different network elements or data centers.
Organizations that fail to protect data in transit are more susceptible to man-in-the-middle attacks, eavesdropping, and session hijacking. These attacks can be the first step attackers use to gain access to confidential data.
For example, the recent NOBELIUM cyberattacks show that no one can be 100 percent protected against a breach. During this attack, 18,000 SolarWinds customers were vulnerable, including Fortune 500 companies and multiple agencies in the US government.
Data in transit should cover two independent encryption mechanisms:
It is recommended customers not only encrypt data on the application layer but also have visibility into their data in transit by using TLS inspection capabilities.
These Microsoft Azure network security services are recommended for this purpose:
As part of the TLS inspection, the above network services perform full decryption and encryption of the traffic, give the ability to utilize intrusion detection and prevention systems (IDPS), as well as providing customers with visibility into the data itself.
To provide customers double encryption when sending data between regions, Azure provides data link layer encryption utilizing media access control security (MACSec).
MACSec is a vendor-independent IEEE Standard (802.1ae), which provides data link layer, point-to-point encryption of traffic between network devices. The packets are encrypted/decrypted on the hardware before being sent and are designed to prevent even a physical “man-in-middle” attack. Because MACSec uses line rate encryption, it can secure data without the performance overhead and complexity of IP encryption technologies such as IPSec/GRE.
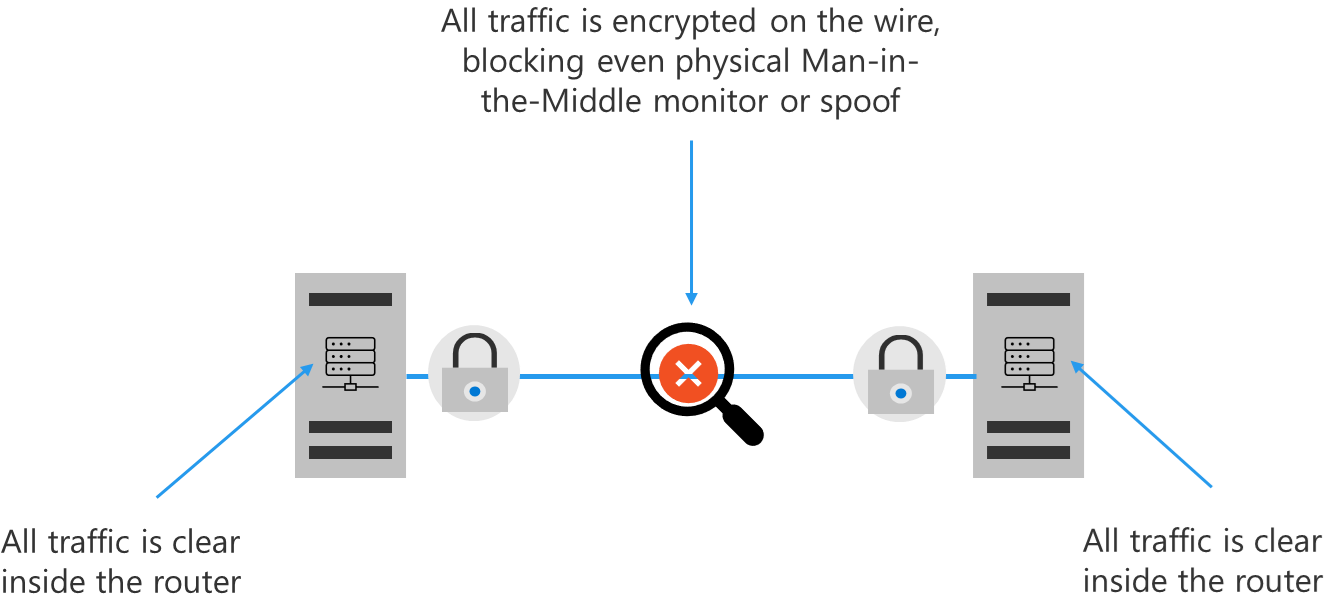
Whenever Azure customer traffic moves between Azure datacenters—outside physical boundaries not controlled by Microsoft (or on behalf of Microsoft)—a data link layer encryption method using the IEEE 802.1AE MAC Security Standards is applied from point-to-point across the underlying network hardware. The packets are encrypted and decrypted on the devices before being sent and applied by default for all Azure traffic traveling within a region or between regions.
We often hear from customers that they are concerned about moving extremely sensitive IP and data to the cloud. To effectively protect assets, not only must data be secured at rest and in transit, but data must also be protected from threats while in use.
To protect data in use for services across your software-as-a-service (SaaS), platform-as-a-service (PaaS), and infrastructure-as-a-service (IaaS) cloud models, we offer two important capabilities: Azure confidential computing and centralized storage of application secrets.
Azure confidential computing encrypts data in memory in hardware-based trusted execution environments (TEEs) and only processes it once the cloud environment is verified, preventing data access from cloud operators, malicious admins, and privileged software such as the hypervisor. By protecting data in use, organizations can achieve the highest levels of data privacy and enable secure multi-party data analytics, without giving access to their data.
These Azure services are recommended to be used for data in use protection:
Protecting your data throughout its lifecycle and wherever it resides or travels is the most critical step to safeguard your business data.
To learn more about the end-to-end implementation of data protection as a critical part of your Zero Trust strategy, visit our Deployment Center.
To see how your organization’s data security posture stacks up against the Zero Trust maturity model, take this interactive quiz.
For more information about a Zero Trust security posture, visit the Microsoft Zero Trust website.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.