| Domain | Registered | Registrar | X.509 TLS Certificate Issuer | DNS provider resolving |
| centralitdef[.]com | 2023/04/03 14:29:33 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| rootgatewayshome[.]com | 2023/04/06 16:09:06 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| directstoragepro[.]com | 2023/04/07 14:18:19 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infocryptoweb[.]com | 2023/04/07 14:44:38 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cloudwebstorage[.]com | 2023/04/09 14:13:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cryptdatahub[.]com | 2023/04/10 10:07:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| datainfosecure[.]com | 2023/04/10 10:16:20 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| servershieldme[.]com | 2023/04/11 07:32:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| scandefinform[.]com | 2023/04/12 10:18:26 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| guardittech[.]com | 2023/04/12 13:36:33 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| storageinfohub[.]com | 2023/04/14 12:23:02 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docsinfohub[.]com | 2023/04/14 16:24:45 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| dbasechecker[.]com | 2023/04/20 08:31:04 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| dbasecheck[.]com | 2023/04/20 08:31:04 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| gaterecord[.]com | 2023/04/25 14:17:14 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| directsgate[.]com | 2023/04/25 14:17:14 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| storageinformationsolutions[.]com | 2023/04/25 15:33:03 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| storagedatadirect[.]com | 2023/04/25 15:33:05 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| informationdoorwaycertificate[.]com | 2023/04/25 17:50:04 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| datagatewaydoc[.]com | 2023/04/25 17:50:37 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| panelittechweb[.]com | 2023/04/27 12:19:19 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| panelitsolution[.]com | 2023/04/27 12:19:19 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| keeperdocument[.]com | 2023/04/27 14:18:19 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| keeperdocumentgatewayhub[.]com | 2023/04/27 14:18:25 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| docview[.]cloud | 2023/05/03 06:33:44 | Hostinger UAB | C=US, O=Let’s Encrypt, CN=R3 | |
| protectitbase[.]com | 2023/05/03 09:07:33 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| webcatalogpro[.]com | 2023/05/04 09:47:19 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infoformdata[.]com | 2023/05/04 13:13:56 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| keydatastorageunit[.]com | 2023/05/10 09:20:39 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docanalizergate[.]com | 2023/05/10 15:23:14 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| docanalizerhub[.]com | 2023/05/10 15:23:21 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| hubdatapage[.]com | 2023/05/10 16:07:31 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| skyinformdata[.]com | 2023/05/11 11:10:35 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docsaccessdata[.]com | 2023/05/11 12:35:02 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| datacryptosafe[.]com | 2023/05/11 16:46:00 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cloudsetupprofi[.]com | 2023/05/12 15:35:42 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| setupprofi[.]com | 2023/05/12 15:35:52 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| analyzedatainfo[.]com | 2023/05/15 15:30:04 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infocryptodata[.]com | 2023/05/15 16:41:42 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| datadocsview[.]com | 2023/05/16 13:23:38 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| gatedocsview[.]com | 2023/05/16 13:23:42 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| hubinfodocs[.]com | 2023/05/16 13:27:07 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| proffsolution[.]com | 2023/05/16 14:20:42 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| proffitsolution[.]com | 2023/05/16 14:20:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| defproresults[.]com | 2023/05/16 14:20:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| greatnotifyinfo[.]com | 2023/05/16 14:55:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| topnotifydata[.]com | 2023/05/16 14:55:53 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| topinformdata[.]com | 2023/05/16 14:55:58 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| defoffresult[.]com | 2023/05/16 15:23:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cloudinfodata[.]com | 2023/05/16 15:23:52 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| webpartdata[.]com | 2023/05/16 15:23:57 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infostoragegate[.]com | 2023/05/17 14:41:37 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| wardenstoragedoorway[.]com | 2023/05/17 15:17:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| myposcheck[.]com | 2023/05/25 08:52:50 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| poscheckdatacenter[.]com | 2023/05/25 08:52:51 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| checkdatapos[.]com | 2023/05/25 08:52:55 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docdatares[.]com | 2023/05/26 13:42:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| datawebhub[.]com | 2023/05/26 16:28:34 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cloudithub[.]com | 2023/05/26 16:28:35 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| secitweb[.]com | 2023/05/26 16:28:39 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| documentitsolution[.]com | 2023/05/29 13:21:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| keeperinformation[.]com | 2023/05/29 13:21:48 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| webprodata[.]com | 2023/05/29 14:28:00 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| clouditprofi[.]com | 2023/05/29 14:28:01 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cryptoinfostorage[.]com | 2023/05/29 14:34:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| rootinformationgateway[.]com | 2023/05/29 14:34:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| gatewaydocumentdata[.]com | 2023/06/01 14:49:07 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| gatewayitservices[.]com | 2023/06/01 14:49:17 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infoviewerdata[.]com | 2023/06/01 14:59:51 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infoviewergate[.]com | 2023/06/01 14:59:51 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| webitresourse[.]com | 2023/06/02 19:35:46 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| homedocsdata[.]com | 2023/06/05 16:05:54 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| homedocsview[.]com | 2023/06/05 16:06:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| webdataproceed[.]com | 2023/06/08 17:29:54 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| directkeeperstorage[.]com | 2023/06/12 15:47:55 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| gatewaykeeperinformation[.]com | 2023/06/12 15:48:01 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| rootgatestorage[.]com | 2023/06/12 16:46:02 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| documentinformationsolution[.]com | 2023/06/12 16:46:04 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| getclouddoc[.]com | 2023/06/14 10:56:38 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| statusfiles[.]com | 2023/06/16 09:49:55 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| webstaticdata[.]com | 2023/06/16 09:49:55 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cloudwebfile[.]com | 2023/06/16 09:49:59 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| statuswebcert[.]com | 2023/06/16 10:29:57 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| nextgenexp[.]com | 2023/06/16 10:29:57 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| informationkeeper[.]com | 2023/06/16 14:48:40 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| documentgatekeeper[.]com | 2023/06/16 14:48:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cryptogatesolution[.]com | 2023/06/16 15:32:31 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| rootgatewaystorage[.]com | 2023/06/16 15:32:34 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infoviewstorage[.]com | 2023/06/22 12:34:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infoconnectstorage[.]com | 2023/06/22 12:34:18 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infolookstorage[.]com | 2023/06/22 13:53:04 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| judicialliquidators[.]com | 2023/06/25 11:28:05 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| safetyagencyservice[.]com | 2023/06/25 11:28:08 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| dynamiclnk[.]com | 2023/06/27 13:20:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| temphoster[.]com | 2023/06/27 13:20:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| documententranceintelligence[.]com | 2023/06/27 17:13:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| documentgateprotector[.]com | 2023/06/27 17:13:51 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| readinfodata[.]com | 2023/06/28 16:09:46 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| readdatainform[.]com | 2023/06/28 16:09:50 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| webcryptoinfo[.]com | 2023/06/29 12:41:50 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| storageinfodata[.]com | 2023/06/29 12:41:50 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| keeperdatastorage[.]com | 2023/07/03 17:40:16 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| keepinformationroot[.]com | 2023/07/03 17:40:21 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| keyservicebar[.]com | 2023/07/05 13:25:41 | PDR Ltd. | C=US, O=Let’s Encrypt, CN=R3 | |
| bitespacedev[.]com | 2023/07/05 13:25:43 | PDR Ltd. | C=US, O=Let’s Encrypt, CN=R3 | |
| cryptodocumentinformation[.]com | 2023/07/05 15:04:46 | PDR Ltd. | C=US, O=Let’s Encrypt, CN=R3 | |
| directdocumentinfo[.]com | 2023/07/05 15:04:48 | PDR Ltd. | C=US, O=Let’s Encrypt, CN=R3 | |
| techpenopen[.]com | 2023/07/05 15:49:13 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| loginformationbreakthrough[.]com | 2023/07/06 16:01:36 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| alldocssolution[.]com | 2023/07/06 16:01:39 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| documentkeepersolutionsystems[.]com | 2023/07/06 18:45:01 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docholdersolution[.]com | 2023/07/06 18:45:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infodocitsolution[.]com | 2023/07/07 11:00:59 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| securebrowssolution[.]com | 2023/07/07 11:00:59 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| secbrowsingate[.]com | 2023/07/07 11:18:09 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| secbrowsingsystems[.]com | 2023/07/07 11:18:14 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docguardmaterial[.]com | 2023/07/10 11:38:40 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| dockeeperweb[.]com | 2023/07/10 11:38:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docsecgate[.]com | 2023/07/11 13:27:59 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| documentsecsolution[.]com | 2023/07/11 13:28:01 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| cryptogatehomes[.]com | 2023/07/11 17:51:38 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| topcryptoprotect[.]com | 2023/07/12 13:03:36 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| safedocumentgatesolution[.]com | 2023/07/12 13:17:15 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| safedocitsolution[.]com | 2023/07/12 13:17:23 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docscontentview[.]com | 2023/07/12 15:05:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| docscontentgate[.]com | 2023/07/12 15:05:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| openprojectgate[.]com | 2023/07/12 15:30:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| infowardendoc[.]com | 2023/07/12 15:30:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| wardensecbreakthrough[.]com | 2023/07/12 15:41:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| lawsystemjudgement[.]com | 2023/07/12 15:41:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| explorewebdata[.]com | 2023/07/13 08:12:07 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| doorwayseclaw[.]com | 2023/07/13 13:22:18 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| entryloginpoint[.]com | 2023/07/13 13:22:22 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| wardenlawsec[.]com | 2023/07/13 14:12:32 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| entrygatebreak[.]com | 2023/07/13 14:12:32 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| digitalworkdata[.]com | 2023/07/13 15:00:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| digitalhubdata[.]com | 2023/07/13 15:00:45 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| craftfilelink[.]com | 2023/07/13 15:31:00 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| createtempdoc[.]com | 2023/07/13 15:31:00 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| provideexplorer[.]com | 2023/07/13 16:25:33 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| reviewopenfile[.]com | 2023/07/13 16:25:34 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| govsafebreakthrough[.]com | 2023/07/13 16:26:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| govlawentrance[.]com | 2023/07/13 16:26:55 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| storagekeepdirect[.]com | 2023/07/13 17:36:39 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| storageguarddirect[.]com | 2023/07/13 17:36:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| storagekeeperexpress[.]com | 2023/07/14 13:27:26 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| onestorageprotectordirect[.]com | 2023/07/14 13:27:27 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| lawwardensafety[.]com | 2023/07/14 13:41:52 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| entrancequick[.]com | 2023/07/14 13:41:53 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| seclawdoorway[.]com | 2023/07/14 15:28:39 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| wardengovermentlaw[.]com | 2023/07/14 15:28:43 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| getvaluepast[.]com | 2023/07/14 16:14:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| transferlinkdata[.]com | 2023/07/14 16:14:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| remcemson[.]com | 2023/07/26 11:25:48 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| osixmals[.]com | 2023/07/26 11:25:56 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| entranceto[.]com | 2023/07/28 12:26:15 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| govermentsecintro[.]com | 2023/07/28 12:26:17 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| itbugreportbeta[.]com | 2023/07/28 13:06:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| theitbugreportbeta[.]com | 2023/07/28 13:06:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| sockintrodoorway[.]com | 2023/07/28 13:21:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| maxintrosec[.]com | 2023/07/28 13:21:42 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| doorgovcommunity[.]com | 2023/07/28 15:11:40 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| tarentrycommunity[.]com | 2023/07/28 15:11:40 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
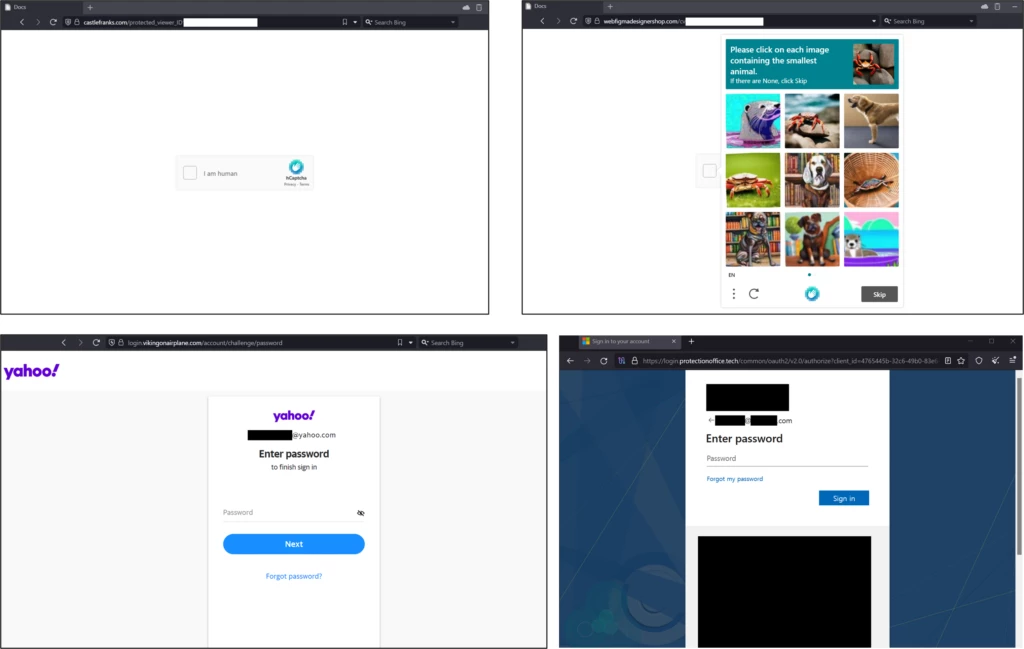
| webfigmadesignershop[.]com | 2023/07/28 16:09:07 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| webfigmadesigner[.]com | 2023/07/28 16:09:11 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| logincontrolway[.]com | 2023/07/28 16:35:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| vertransmitcontrol[.]com | 2023/07/28 16:35:44 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| everyinit[.]com | 2023/08/09 13:56:51 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| aliceplants[.]com | 2023/08/09 17:22:26 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| countingtall[.]com | 2023/08/09 17:22:30 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| silenceprotocol[.]com | 2023/08/10 12:32:10 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| mintwithapples[.]com | 2023/08/10 12:32:15 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| winterholds[.]com | 2023/08/10 12:53:29 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| ziplinetransfer[.]com | 2023/08/10 16:47:53 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| translatesplit[.]com | 2023/08/10 16:47:53 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| getfigmacreator[.]com | 2023/08/11 13:13:20 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| postrequestin[.]com | 2023/08/11 13:13:23 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| tarifjane[.]com | 2023/08/17 14:05:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| configlayers[.]com | 2023/08/17 14:05:48 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| winterhascometo[.]com | 2023/08/17 16:21:43 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| inyourheadexp[.]com | 2023/08/17 16:21:43 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| glorybuses[.]com | 2023/08/18 15:27:40 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| janeairintroduction[.]com | 2023/08/18 15:27:40 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| vikingonairplane[.]com | 2023/08/18 16:19:48 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| marungame[.]com | 2023/08/18 16:19:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| victorinwounder[.]com | 2023/08/21 16:14:48 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| paneindestination[.]com | 2023/08/21 16:15:02 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| trastamarafamily[.]com | 2023/08/22 11:20:22 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| territoryedit[.]com | 2023/08/22 11:20:24 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| vectorto[.]com | 2023/08/24 09:40:49 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| johnysadventure[.]com | 2023/08/24 09:40:54 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| paternenabler[.]com | 2023/08/25 14:40:31 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| fastnamegenerator[.]com | 2023/08/25 14:40:35 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| literallyandme[.]com | 2023/08/28 13:21:33 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| andysalesproject[.]com | 2023/08/28 13:21:34 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| pandawithrainbow[.]com | 2023/08/28 17:08:58 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| natalyincity[.]com | 2023/08/29 15:25:02 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| machinerelise[.]com | 2023/09/01 16:29:09 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| industrialcorptruncate[.]com | 2023/09/01 16:30:07 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| constructionholdingnewlife[.]com | 2023/09/07 14:00:55 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| adventuresrebornpanda[.]com | 2023/09/07 14:00:55 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| cryingpand[.]com | 2023/09/13 13:10:40 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| industrialwatership[.]com | 2023/09/13 13:10:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| olohaisland[.]com | 2023/09/13 14:25:35 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| voodoomagician[.]com | 2023/09/13 14:25:36 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| newestchairs[.]com | 2023/09/14 11:24:47 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| cpuisocutter[.]com | 2023/09/14 12:37:53 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| incorpcpu[.]com | 2023/09/14 12:37:57 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| gulperfish[.]com | 2023/09/14 14:00:25 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| leviathanfish[.]com | 2023/09/14 14:00:25 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| truncationcorp[.]com | 2023/09/14 14:05:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| gzipinteraction[.]com | 2023/09/14 14:05:42 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| ghostshowing[.]com | 2023/09/14 16:10:42 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| hallowenwitch[.]com | 2023/09/14 16:10:43 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| certificatentrance[.]com | 2023/09/19 08:18:39 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| apiwebdata[.]com | 2023/10/02 14:59:14 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| apidatahook[.]com | 2023/10/04 15:45:19 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| apireflection[.]com | 2023/10/04 15:45:25 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| protectionoffice[.]tech | 2023/10/05 11:33:46 | Hostinger UAB | C=US, O=Let’s Encrypt, CN=R3 | |
| lazyprotype[.]com | 2023/10/11 11:52:18 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| angelicfish[.]com | 2023/10/13 17:57:29 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| globalyfish[.]com | 2023/10/13 17:57:31 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| medicprognosis[.]com | 2023/10/16 14:36:32 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| medicoutpatient[.]com | 2023/10/16 14:36:41 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| krakfish[.]com | 2023/10/17 17:09:29 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| stingrayfish[.]com | 2023/10/17 17:09:31 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| incorpreview[.]com | 2023/10/17 18:27:09 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| truncatetrim[.]com | 2023/10/17 18:27:11 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| corporatesinvitation[.]com | 2023/10/18 14:48:54 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| triminget[.]com | 2023/10/18 17:31:40 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| firewitches[.]com | 2023/10/19 10:40:51 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| solartemplar[.]com | 2023/10/19 10:40:52 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
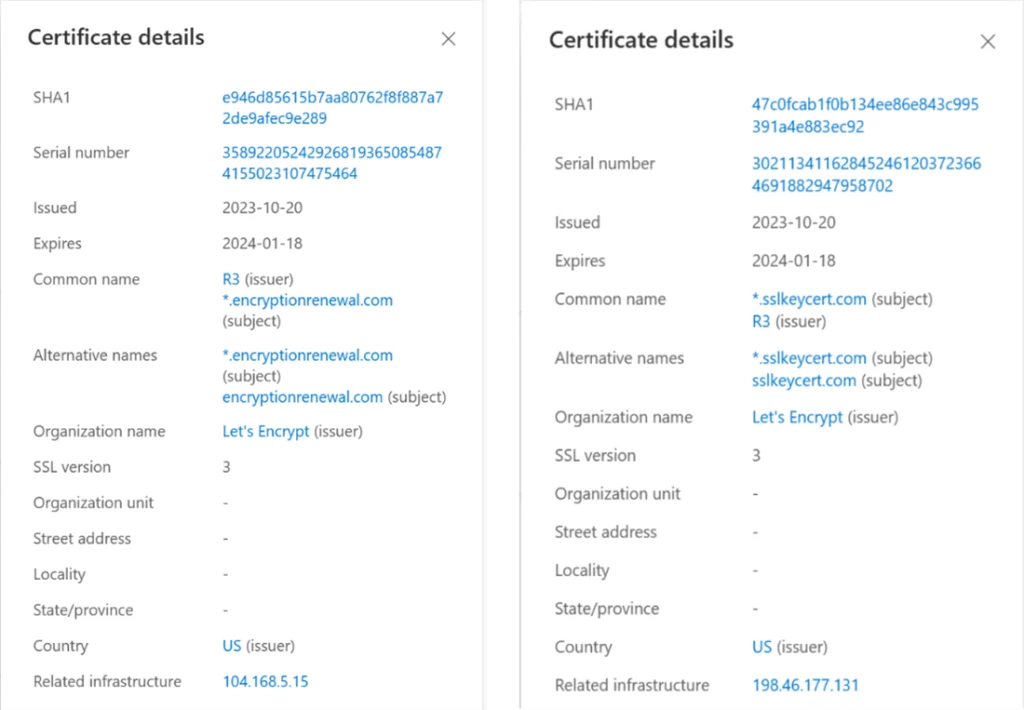
| encryptionrenewal[.]com | 2023/10/20 13:36:24 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| sslkeycert[.]com | 2023/10/20 13:36:24 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| barbarictruths[.]com | 2023/10/23 07:37:30 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| castlefranks[.]com | 2023/10/23 07:37:33 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | Yes |
| comintroduction[.]com | 2023/10/24 14:01:11 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |
| corpviewer[.]com | 2023/10/31 13:10:38 | NameCheap, Inc | C=US, O=Let’s Encrypt, CN=R3 | |